 Image 1 of 7
Image 1 of 7
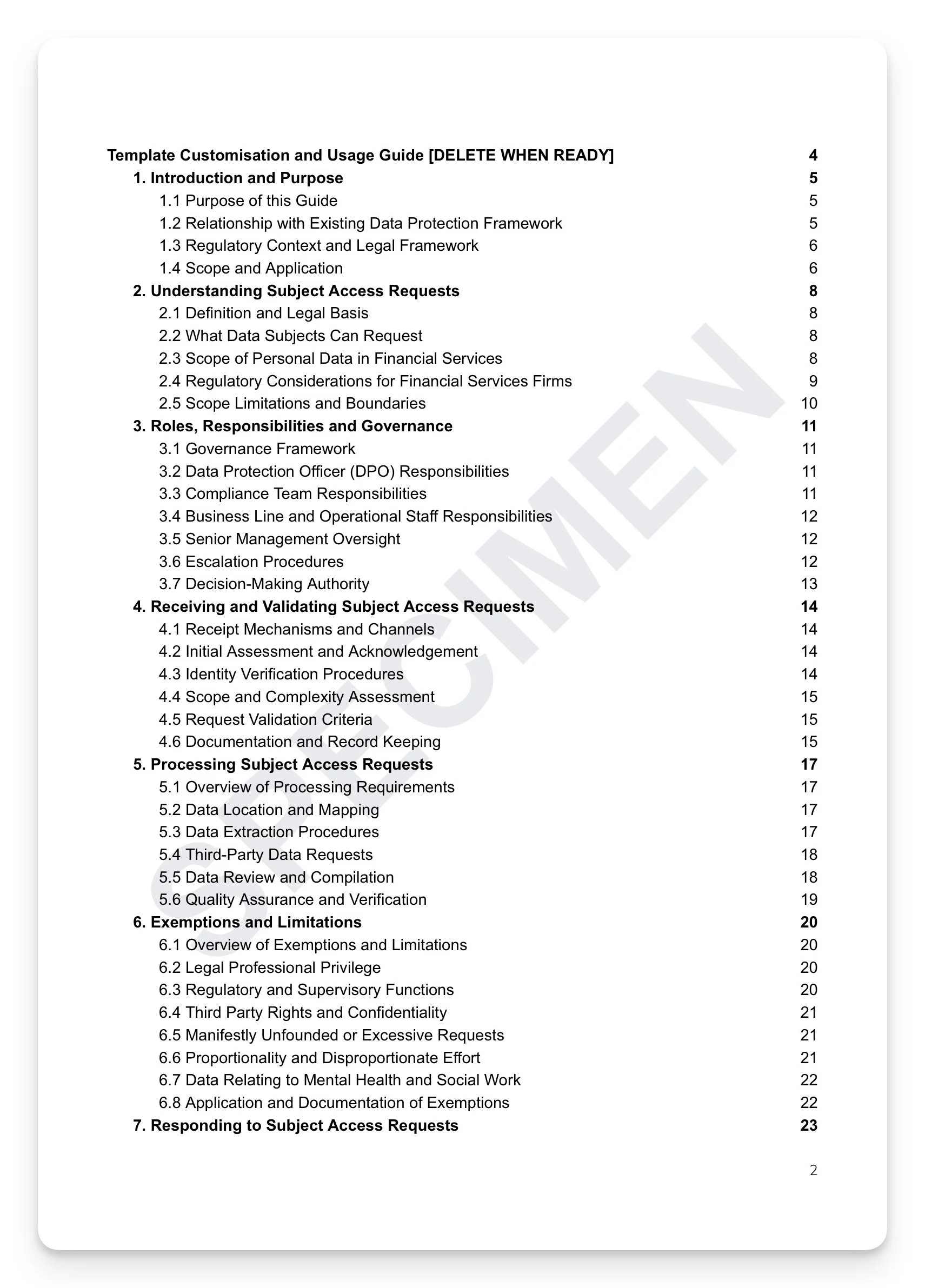 Image 2 of 7
Image 2 of 7
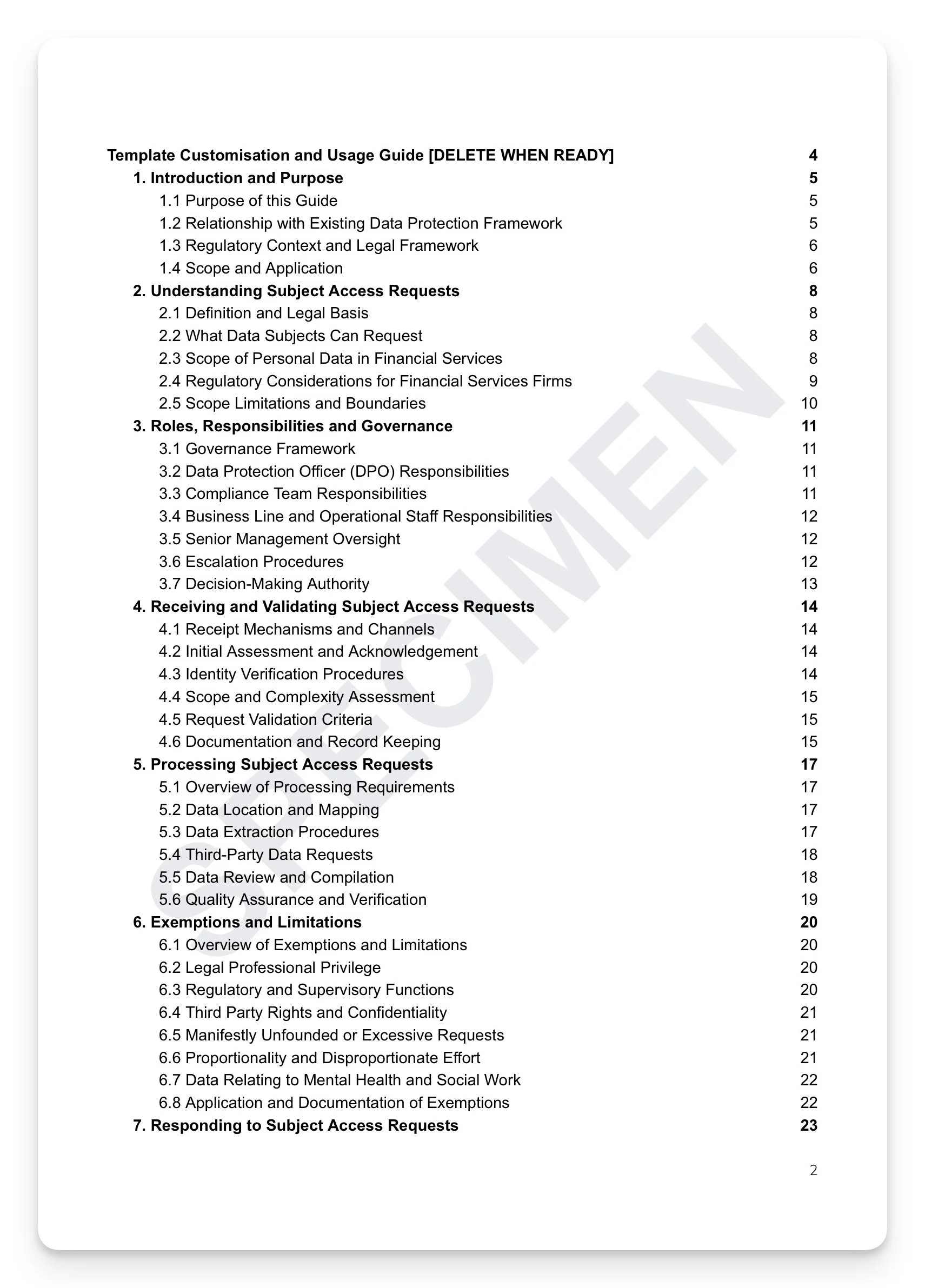
 Image 3 of 7
Image 3 of 7
 Image 4 of 7
Image 4 of 7
 Image 5 of 7
Image 5 of 7
 Image 6 of 7
Image 6 of 7
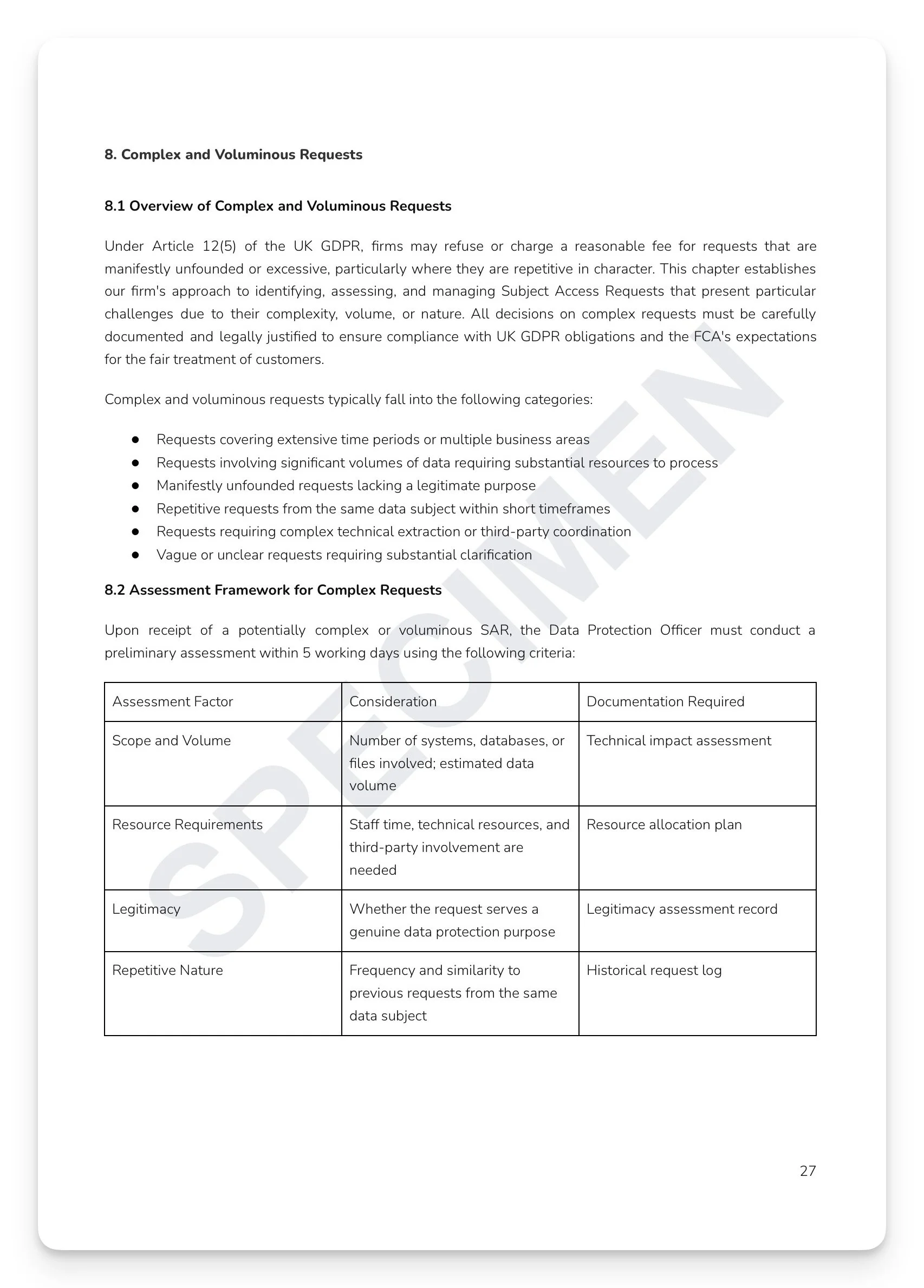
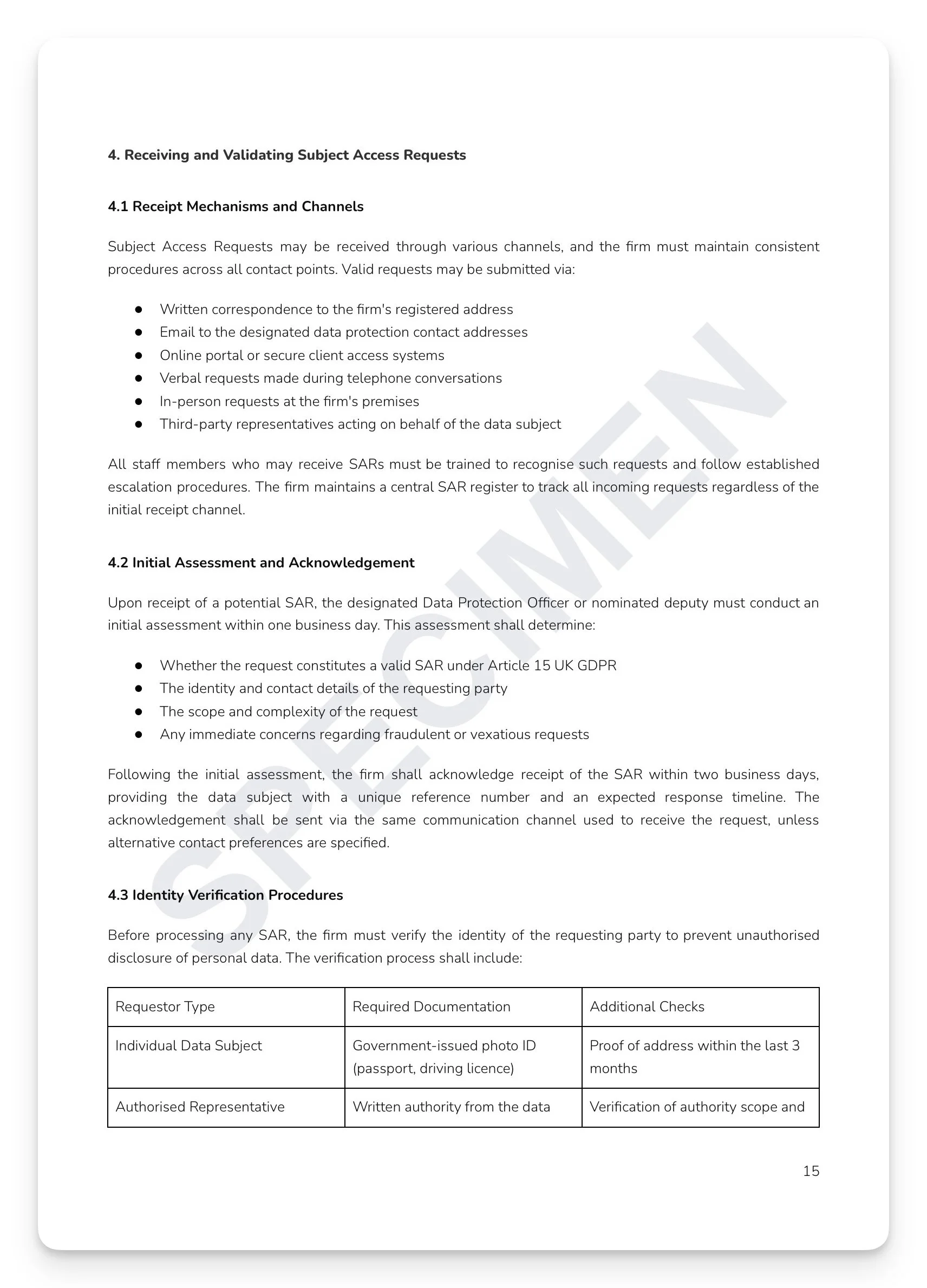 Image 7 of 7
Image 7 of 7
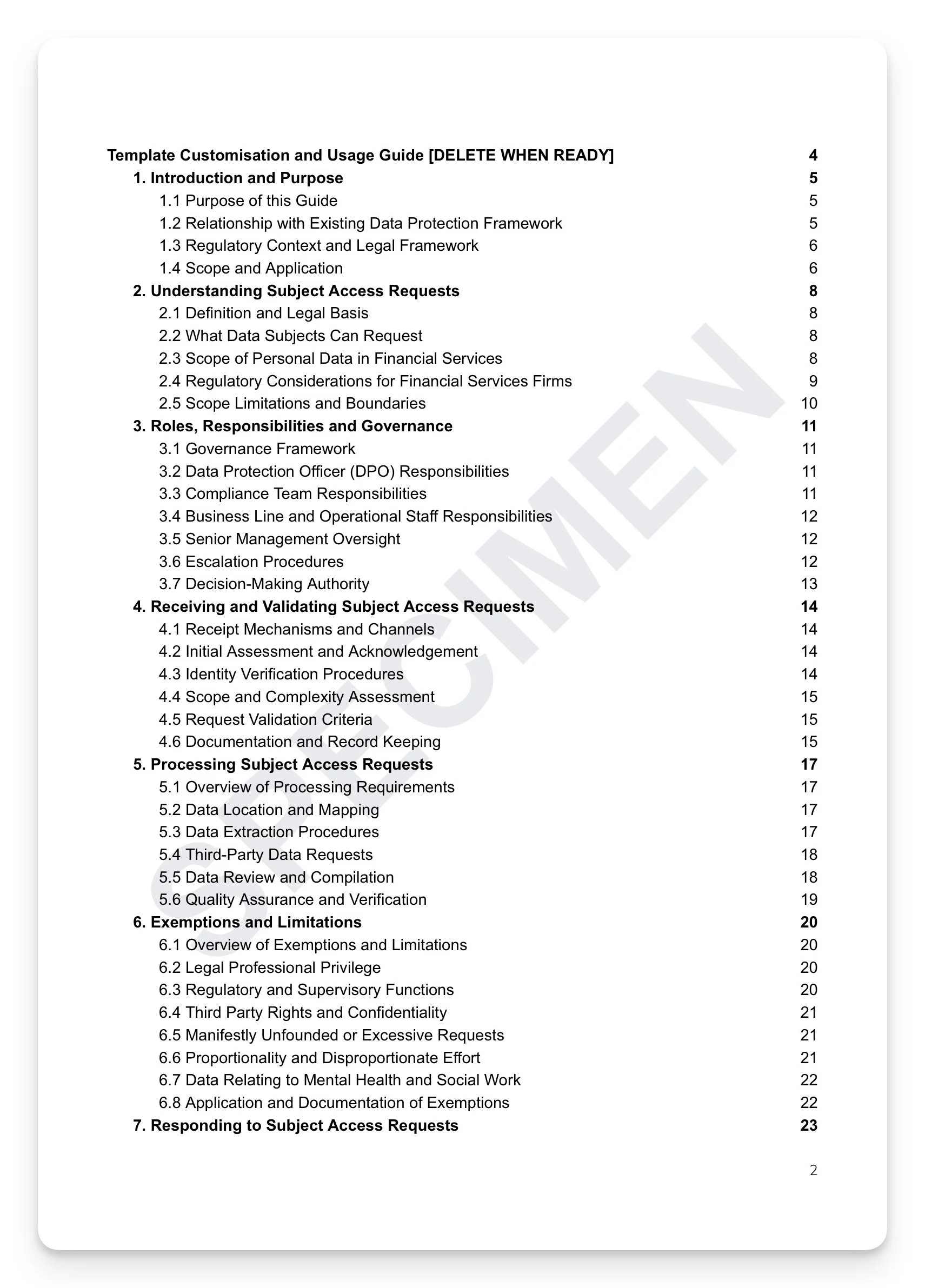
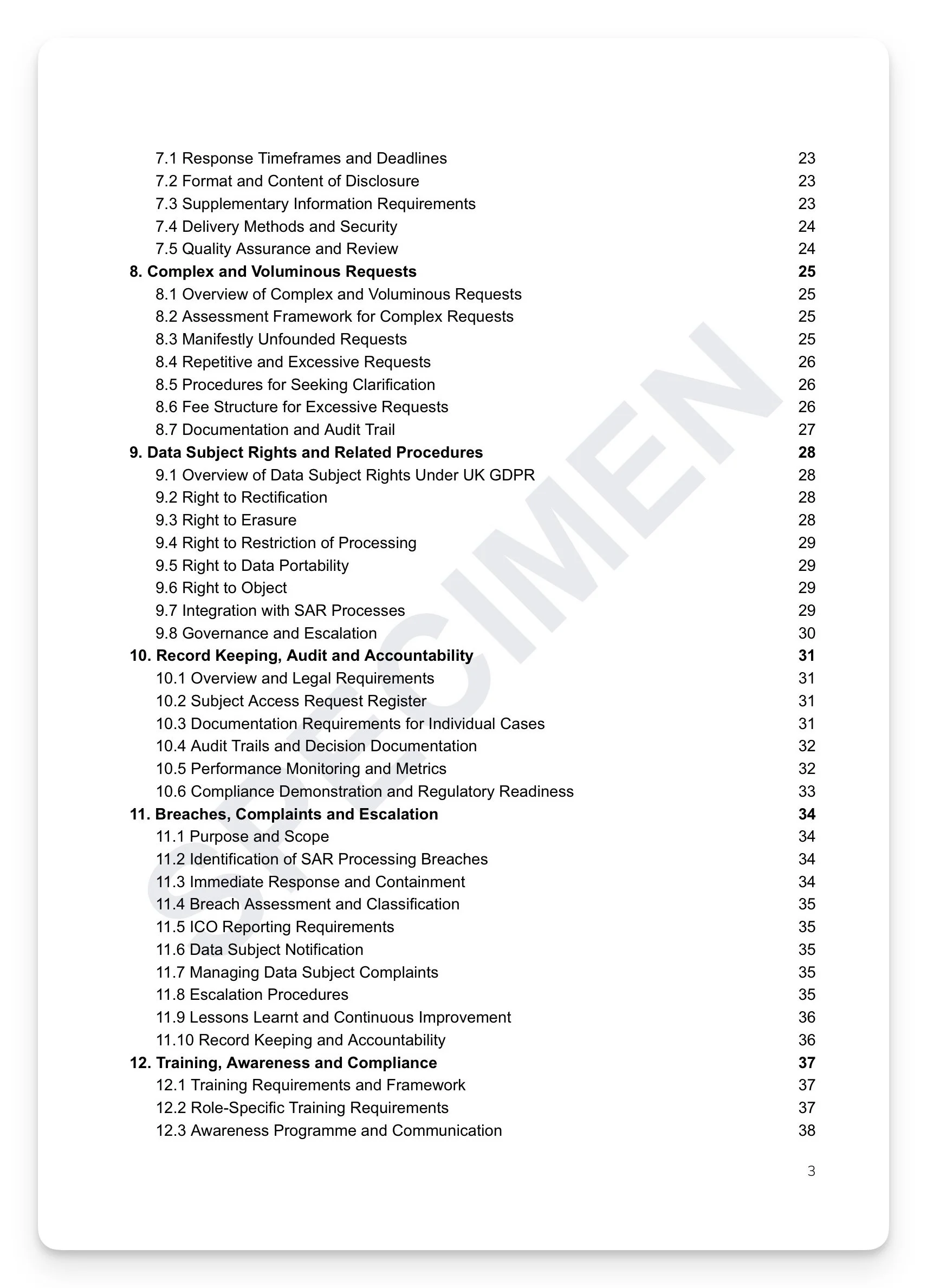
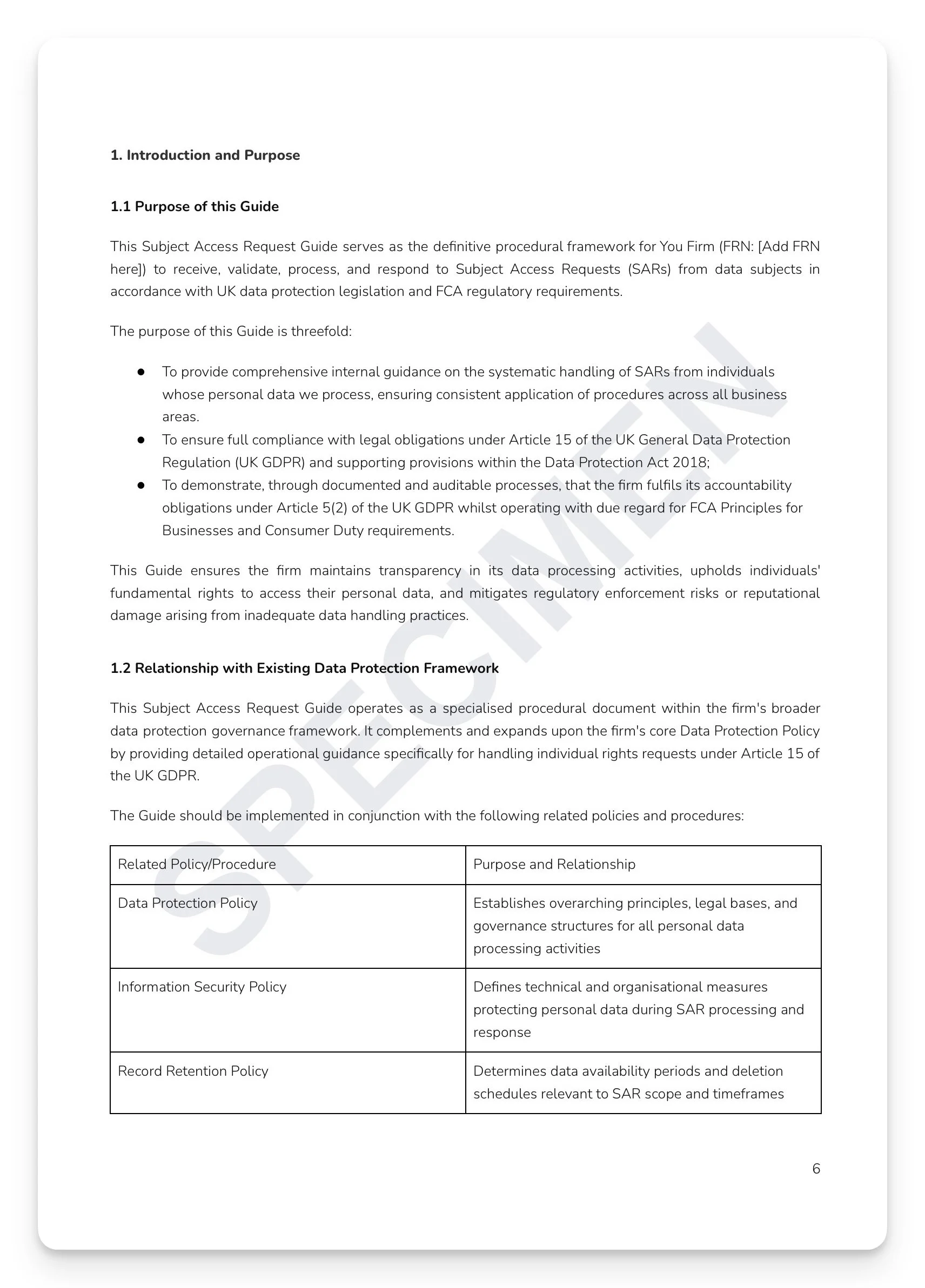
Subject Access Request Manual (Handling Guide)
A SAR form gets the request in. This guide makes sure you don't breach the law when handling it. Under UK GDPR, firms have one month to respond to a Subject Access Request — but the legal exposure doesn't come from missing the deadline alone. It comes from inadequate identity verification, misapplied exemptions, incomplete data mapping, insecure delivery, and undocumented decision-making. The ICO can fine up to £17.5 million or 4% of global turnover, and for FCA-regulated firms, a systemic SAR failure is simultaneously a data protection breach and a governance failure. Most firms have a SAR form. Few have the operational framework behind it.
What's included:
Three-tier governance framework: strategic, operational, and execution — with DPO, compliance team, and business line responsibilities matrix and a central SAR register with one-business-day initial assessment requirement
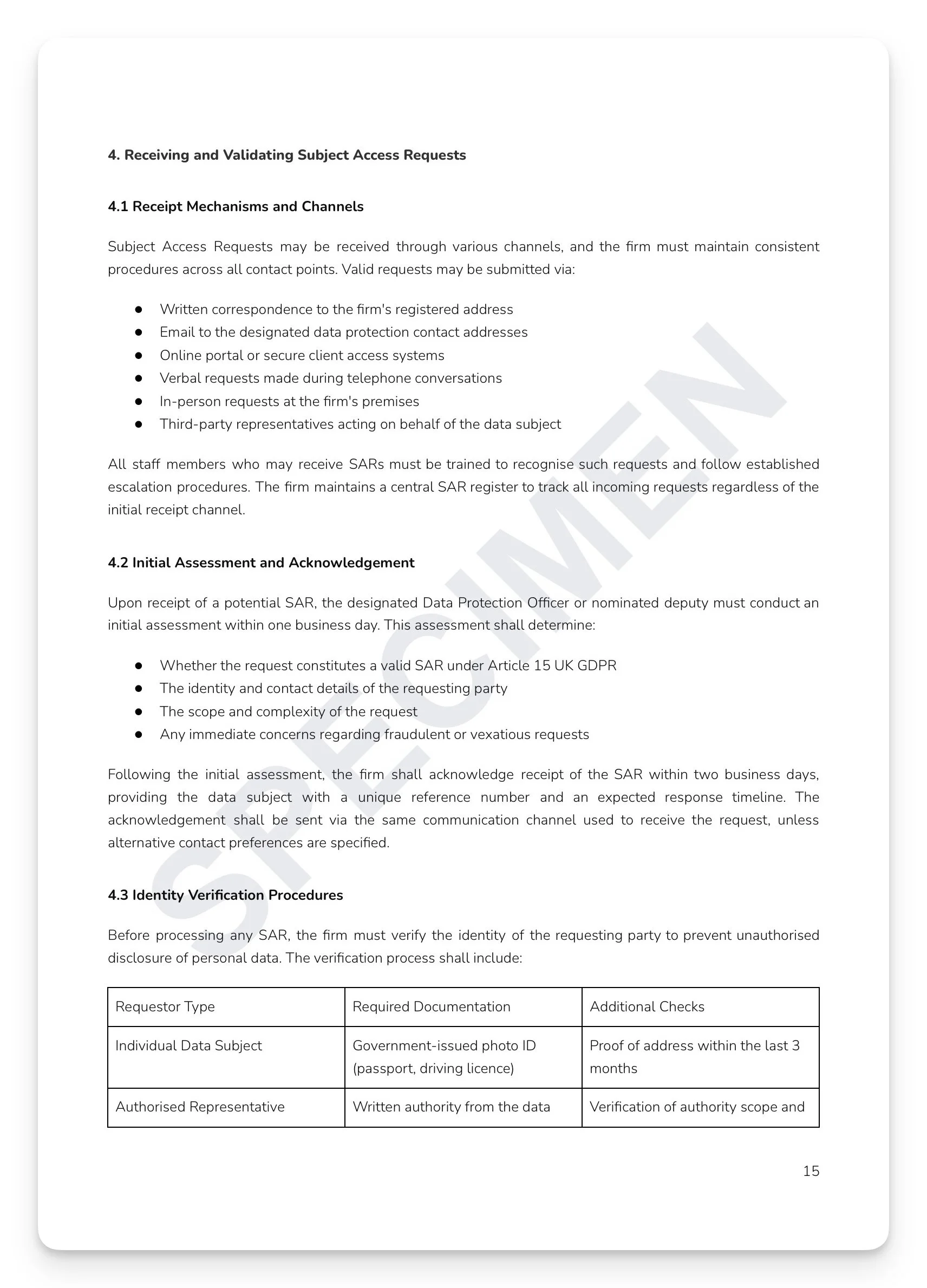
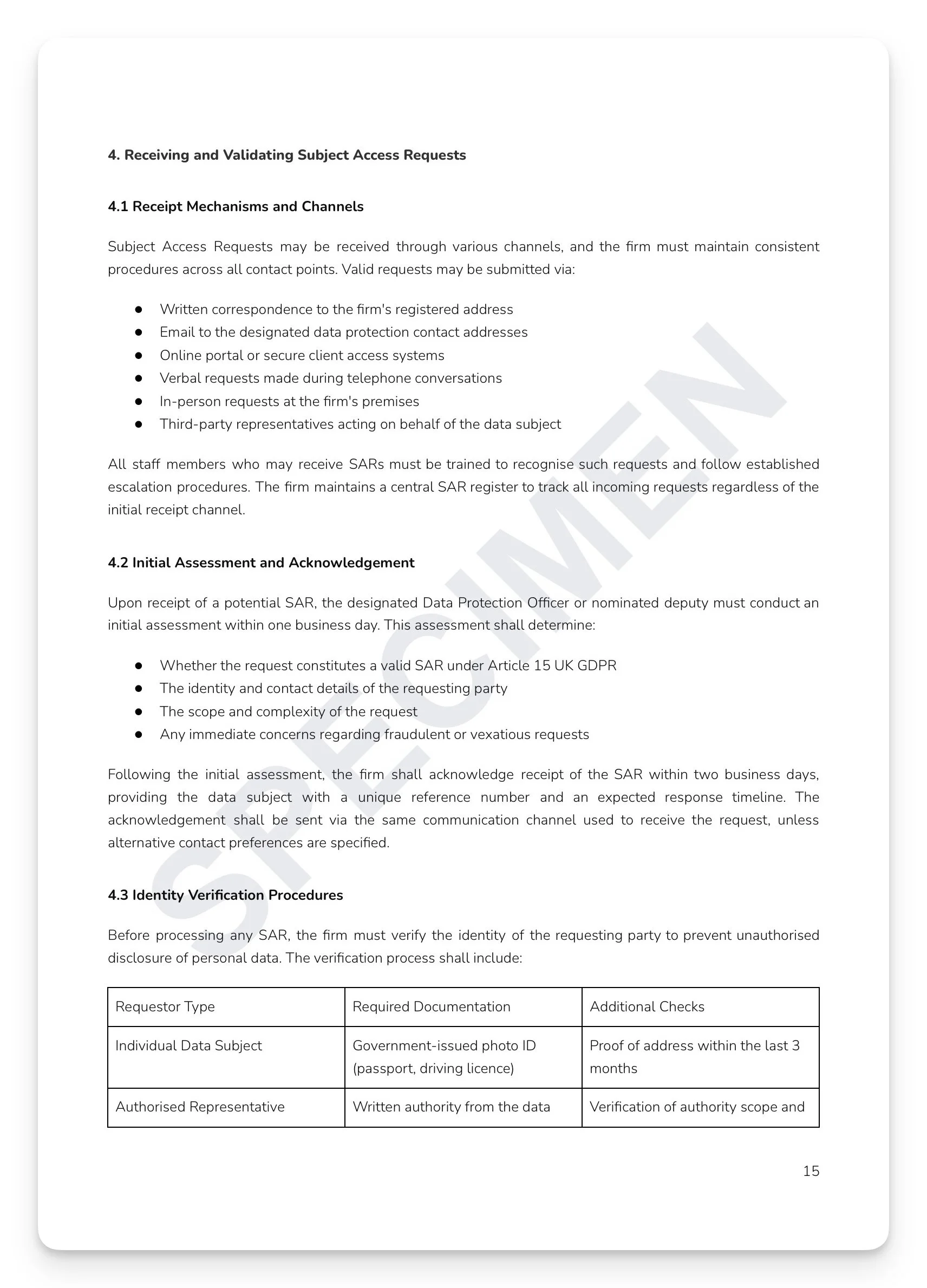
Identity verification matrix by requestor type: individual, representative, LPA, and executor — with standard, complex, and voluminous request categorisation framework
Data location and mapping across all system types: CRM, email, AML, CCTV, backups, and third-party processors — with data extraction procedures and security controls by system type
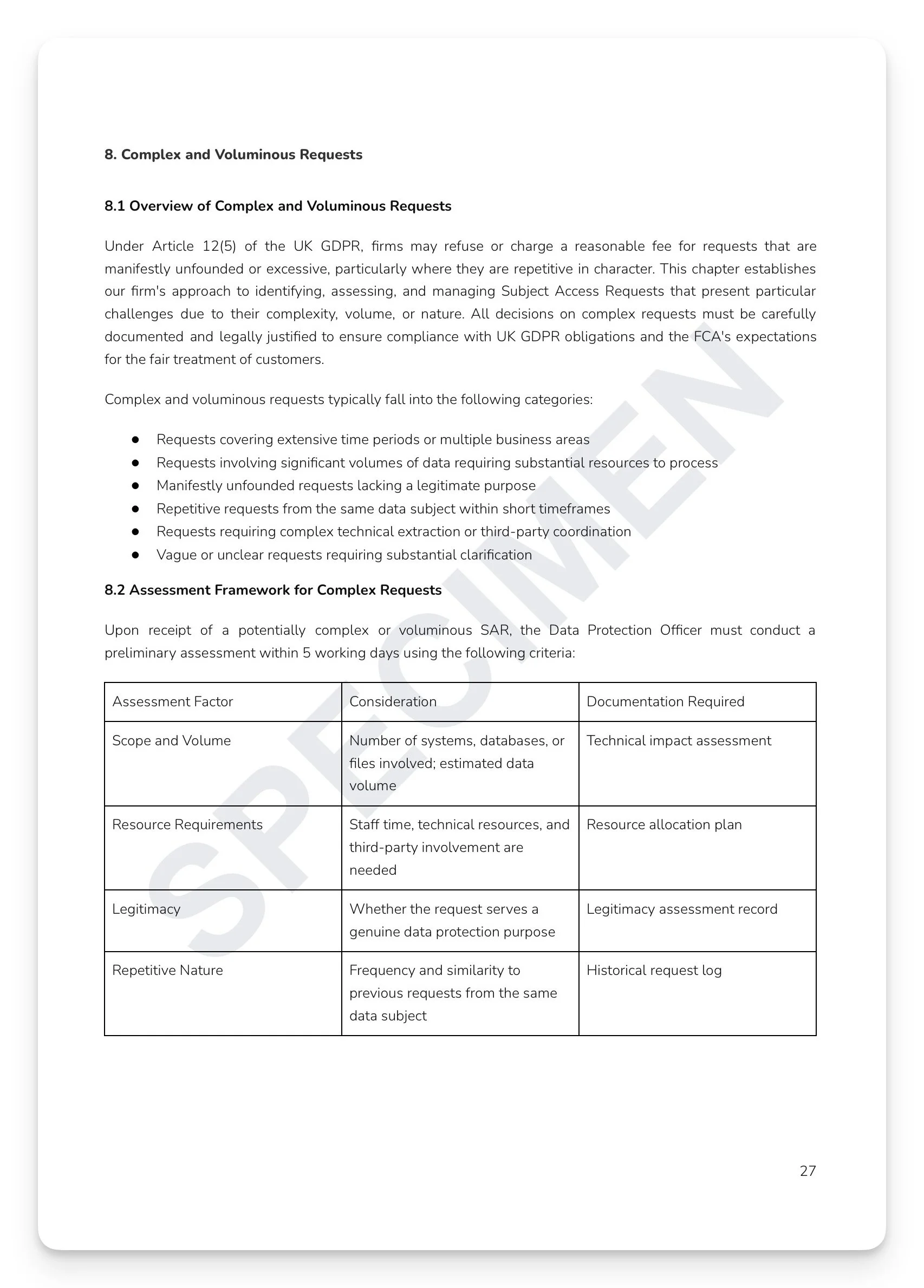
Exemptions guide: legal professional privilege, regulatory functions, and Schedule 2 DPA 2018 — with manifestly unfounded and excessive request assessment and fee structure
One-month response framework: clarification request procedures, two-month extension procedure, quality assurance review before dispatch, and secure delivery methods (encrypted email, registered post, and in-person)
Breach severity classification matrix: Critical through Low — with 72-hour ICO notification procedure, 2-hour DPO notification trigger, and 15-business-day complaint response framework
All six complementary rights integration: Articles 16–22 — with six-year case file retention standard and quarterly compliance monitoring
+ much more
Who is this for?
Data Protection Officers, compliance teams, and senior management at FCA-regulated firms who need a complete, defensible, auditable internal SAR handling process — from receipt and identity verification through data mapping, exemption application, and breach response.
How it works
Step 1 — Read it. Every section exists for a reason, grounded in a specific regulatory obligation.
Step 2 — Understand it. Map the content against your current practices. Identify where you're strong and where gaps exist.
Step 3 — Make it yours. Tailor the language to reflect how your organisation actually operates. A policy that sounds like your firm is a policy your people will follow.
Step 4 — Take ownership. Assign clear accountability — Board approval, named SMF holder, designated policy owner. A policy without an owner is a liability, not an asset.
Step 5 — Operationalise it. Embed the policy into your governance calendar, training programme, and annual review cycle. This is where compliance becomes culture.
Or, get this free with RegTechPRO
Access this alongside the full compliance policy library — SM&CR, COBS, AML, Consumer Duty, GDPR, and more — for a fraction of the cost of consultancy.
A SAR form gets the request in. This guide makes sure you don't breach the law when handling it. Under UK GDPR, firms have one month to respond to a Subject Access Request — but the legal exposure doesn't come from missing the deadline alone. It comes from inadequate identity verification, misapplied exemptions, incomplete data mapping, insecure delivery, and undocumented decision-making. The ICO can fine up to £17.5 million or 4% of global turnover, and for FCA-regulated firms, a systemic SAR failure is simultaneously a data protection breach and a governance failure. Most firms have a SAR form. Few have the operational framework behind it.
What's included:
Three-tier governance framework: strategic, operational, and execution — with DPO, compliance team, and business line responsibilities matrix and a central SAR register with one-business-day initial assessment requirement
Identity verification matrix by requestor type: individual, representative, LPA, and executor — with standard, complex, and voluminous request categorisation framework
Data location and mapping across all system types: CRM, email, AML, CCTV, backups, and third-party processors — with data extraction procedures and security controls by system type
Exemptions guide: legal professional privilege, regulatory functions, and Schedule 2 DPA 2018 — with manifestly unfounded and excessive request assessment and fee structure
One-month response framework: clarification request procedures, two-month extension procedure, quality assurance review before dispatch, and secure delivery methods (encrypted email, registered post, and in-person)
Breach severity classification matrix: Critical through Low — with 72-hour ICO notification procedure, 2-hour DPO notification trigger, and 15-business-day complaint response framework
All six complementary rights integration: Articles 16–22 — with six-year case file retention standard and quarterly compliance monitoring
+ much more
Who is this for?
Data Protection Officers, compliance teams, and senior management at FCA-regulated firms who need a complete, defensible, auditable internal SAR handling process — from receipt and identity verification through data mapping, exemption application, and breach response.
How it works
Step 1 — Read it. Every section exists for a reason, grounded in a specific regulatory obligation.
Step 2 — Understand it. Map the content against your current practices. Identify where you're strong and where gaps exist.
Step 3 — Make it yours. Tailor the language to reflect how your organisation actually operates. A policy that sounds like your firm is a policy your people will follow.
Step 4 — Take ownership. Assign clear accountability — Board approval, named SMF holder, designated policy owner. A policy without an owner is a liability, not an asset.
Step 5 — Operationalise it. Embed the policy into your governance calendar, training programme, and annual review cycle. This is where compliance becomes culture.
Or, get this free with RegTechPRO
Access this alongside the full compliance policy library — SM&CR, COBS, AML, Consumer Duty, GDPR, and more — for a fraction of the cost of consultancy.