 Image 1 of 7
Image 1 of 7
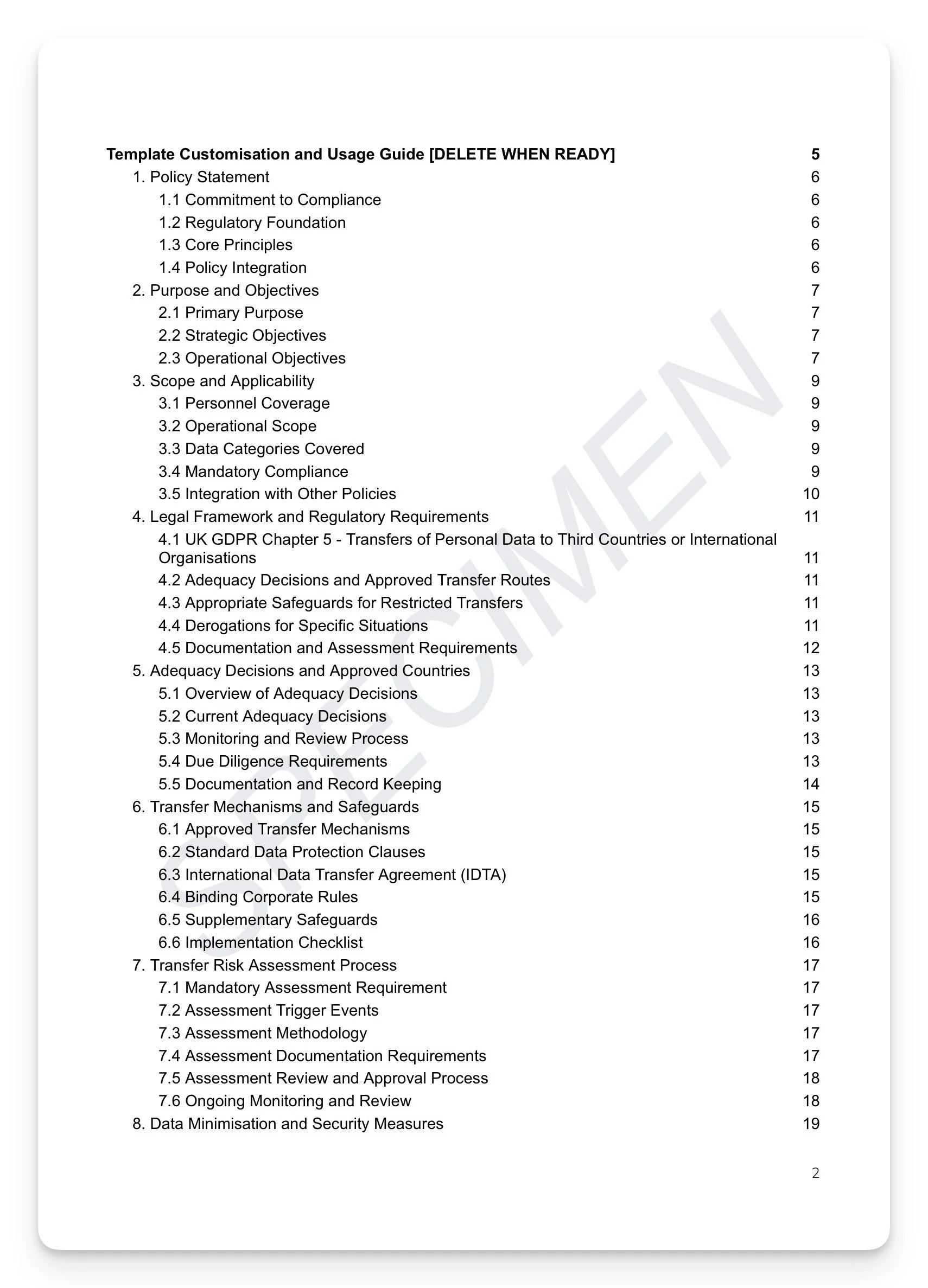 Image 2 of 7
Image 2 of 7
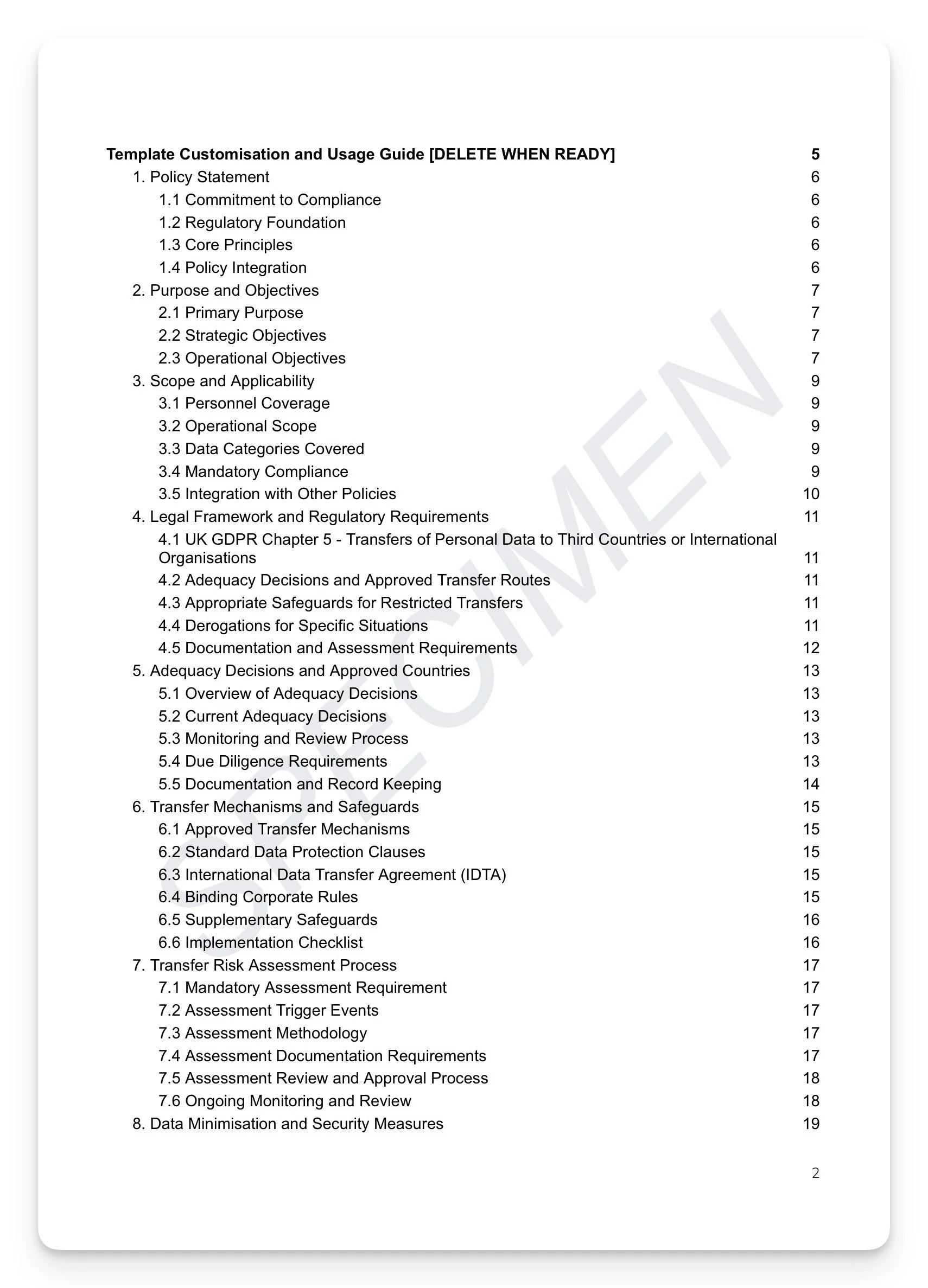
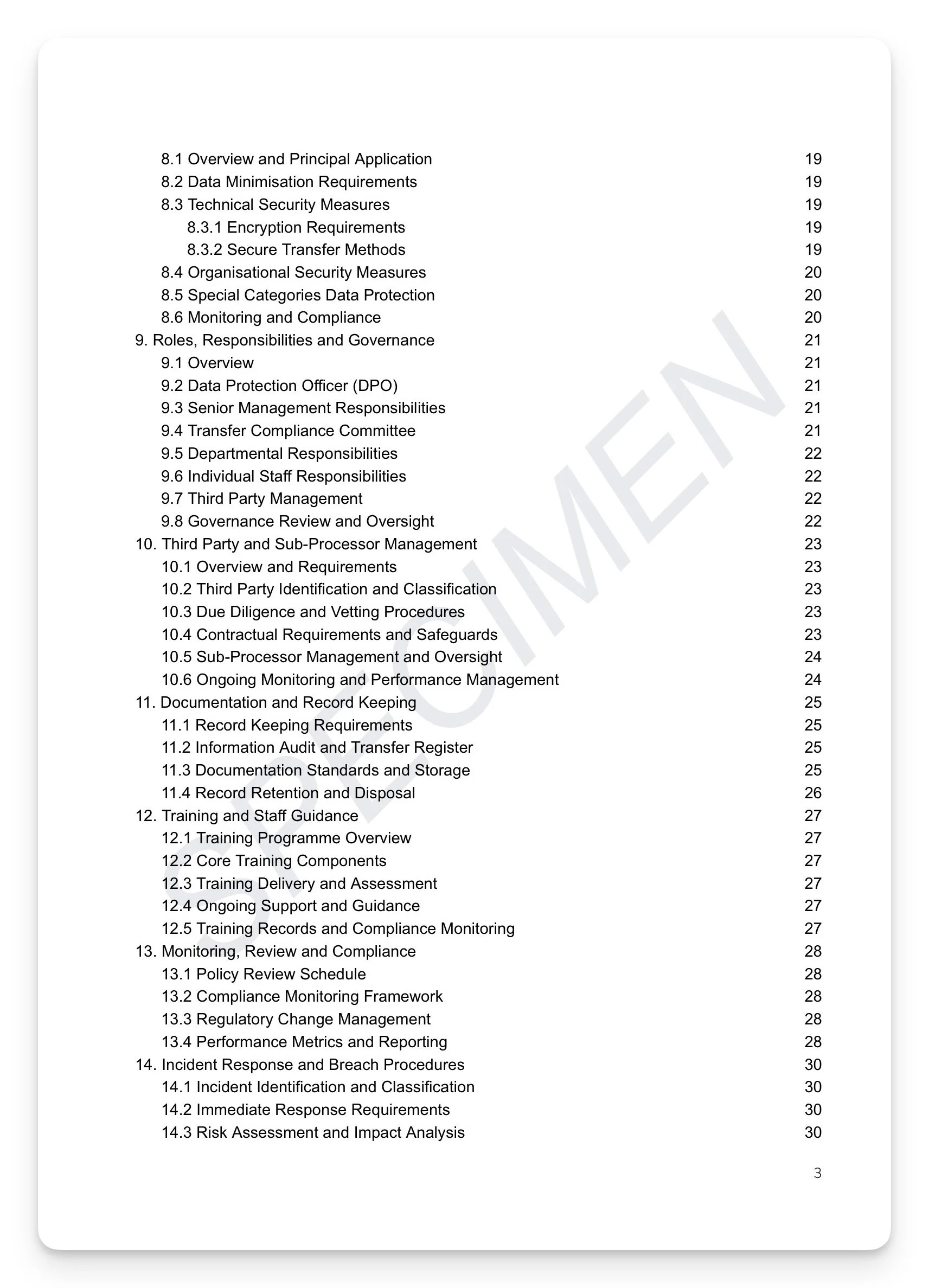 Image 3 of 7
Image 3 of 7
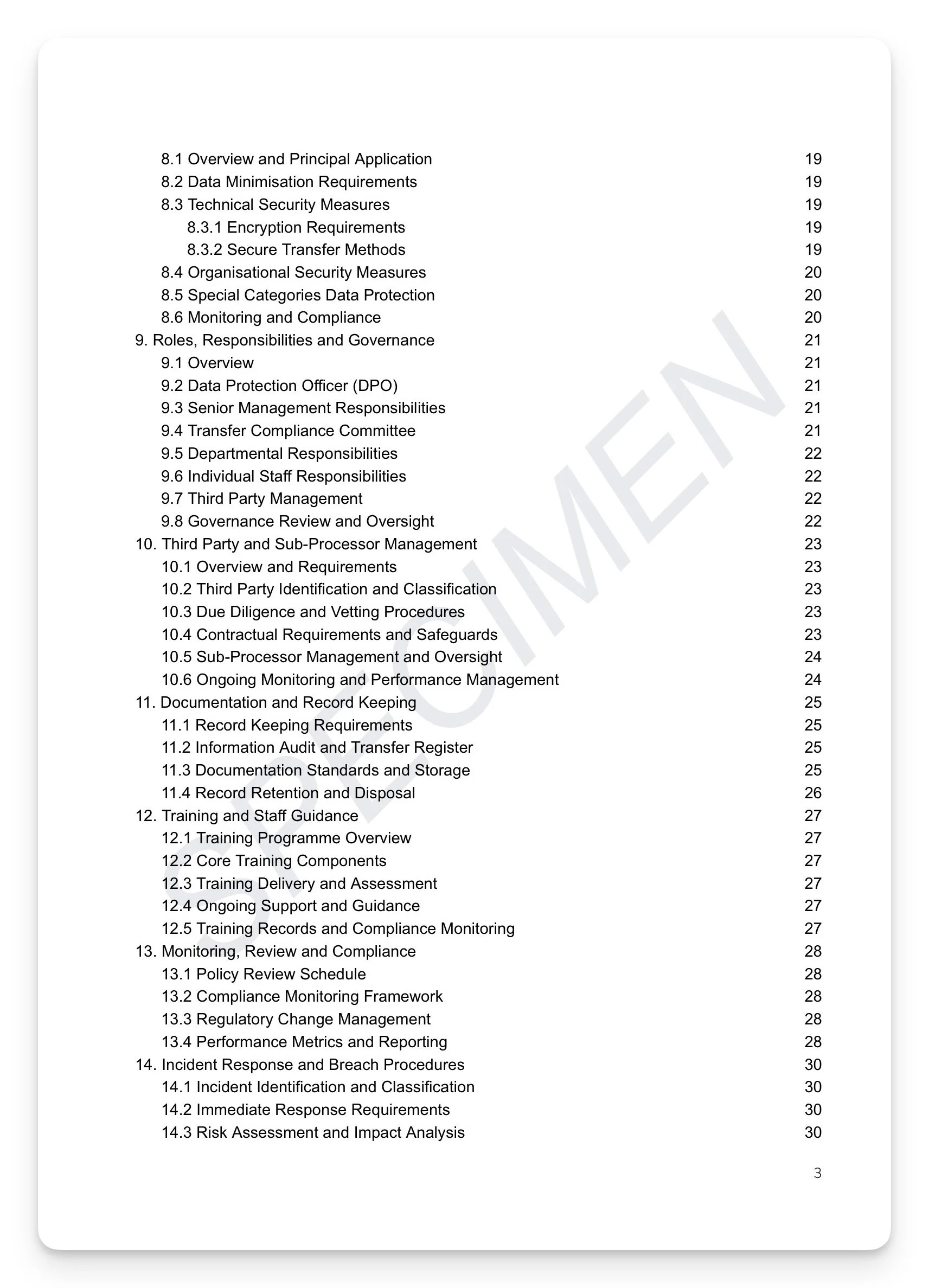
 Image 4 of 7
Image 4 of 7
 Image 5 of 7
Image 5 of 7
 Image 6 of 7
Image 6 of 7
 Image 7 of 7
Image 7 of 7
International Data Transfers Policy Template
Every cloud service, every overseas processor, every cross-border email is a regulated transfer. Under UK GDPR Article 44, transferring personal data outside the UK without a valid legal basis isn't a technical oversight — it's a breach. Most FCA-regulated firms transfer data internationally every day through cloud platforms, outsourced services, and group company arrangements, often without realising it. Without a documented framework, you can't demonstrate compliance, defend a transfer decision, or respond to an ICO inquiry.
What's included:
UK GDPR Chapter 5 (Articles 44–50) compliance framework with current adequacy decision register: EEA, Andorra, Japan, South Korea, US Data Privacy Framework, and more — with monthly adequacy monitoring procedures
Approved transfer mechanisms: SCCs, IDTA, BCRs, and certification — with IDTA implementation requirements and AES-256 encryption and SFTP/VPN secure transfer standards
Transfer Risk Assessment methodology: 23-working-day multi-stage TRA governance process with Transfer Compliance Committee structure and Departmental Transfer Coordinator responsibilities
Special category data enhanced transfer controls — with third-party and sub-processor due diligence, vetting, and contractual safeguards requirements
Incident response framework: 2-hour internal notification trigger, ICO 72-hour breach notification procedures, severity classification matrix, and International Transfer Incident Response Team structure
Transfer register and documentation standards with quarterly performance metrics and KPI dashboard
Comprehensive appendices: TRA form, transfer mechanisms checklist, self-assessment tool, and emergency contacts
+ much more
Who is this for?
Data Protection Officers, Compliance Officers, IT security teams, and legal counsel at FCA-regulated firms with cloud-based operations, overseas processors, or group company structures who need a complete, documented framework for every cross-border data transfer they make.
How it works
Step 1 — Read it. Every section exists for a reason, grounded in a specific regulatory obligation.
Step 2 — Understand it. Map the content against your current practices. Identify where you're strong and where gaps exist.
Step 3 — Make it yours. Tailor the language to reflect how your organisation actually operates. A policy that sounds like your firm is a policy your people will follow.
Step 4 — Take ownership. Assign clear accountability — Board approval, named SMF holder, designated policy owner. A policy without an owner is a liability, not an asset.
Step 5 — Operationalise it. Embed the policy into your governance calendar, training programme, and annual review cycle. This is where compliance becomes culture.
Or, get this free with RegTechPRO
Access this alongside the full compliance policy library — SM&CR, COBS, AML, Consumer Duty, GDPR, and more — for a fraction of the cost of consultancy.
Every cloud service, every overseas processor, every cross-border email is a regulated transfer. Under UK GDPR Article 44, transferring personal data outside the UK without a valid legal basis isn't a technical oversight — it's a breach. Most FCA-regulated firms transfer data internationally every day through cloud platforms, outsourced services, and group company arrangements, often without realising it. Without a documented framework, you can't demonstrate compliance, defend a transfer decision, or respond to an ICO inquiry.
What's included:
UK GDPR Chapter 5 (Articles 44–50) compliance framework with current adequacy decision register: EEA, Andorra, Japan, South Korea, US Data Privacy Framework, and more — with monthly adequacy monitoring procedures
Approved transfer mechanisms: SCCs, IDTA, BCRs, and certification — with IDTA implementation requirements and AES-256 encryption and SFTP/VPN secure transfer standards
Transfer Risk Assessment methodology: 23-working-day multi-stage TRA governance process with Transfer Compliance Committee structure and Departmental Transfer Coordinator responsibilities
Special category data enhanced transfer controls — with third-party and sub-processor due diligence, vetting, and contractual safeguards requirements
Incident response framework: 2-hour internal notification trigger, ICO 72-hour breach notification procedures, severity classification matrix, and International Transfer Incident Response Team structure
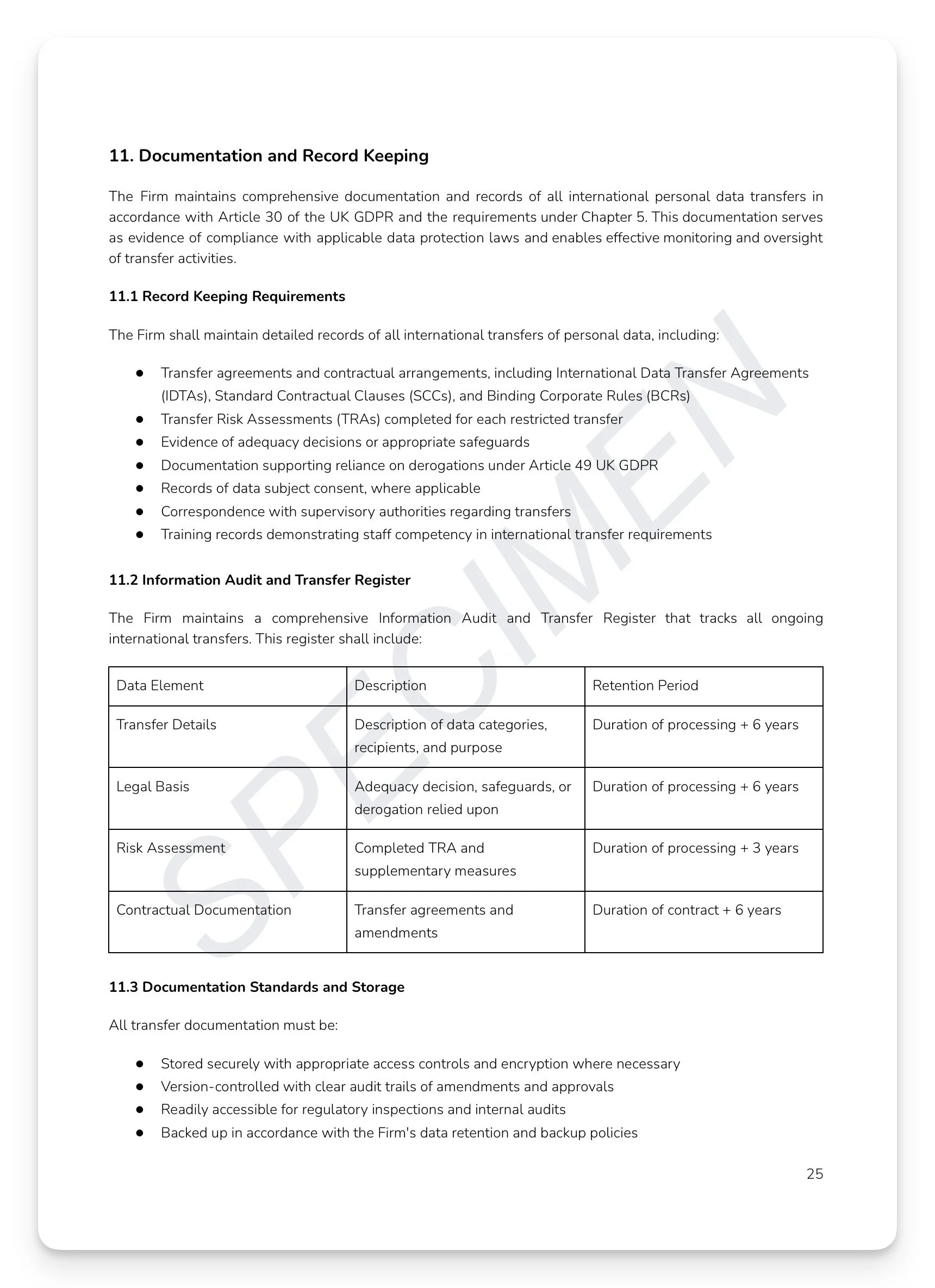
Transfer register and documentation standards with quarterly performance metrics and KPI dashboard
Comprehensive appendices: TRA form, transfer mechanisms checklist, self-assessment tool, and emergency contacts
+ much more
Who is this for?
Data Protection Officers, Compliance Officers, IT security teams, and legal counsel at FCA-regulated firms with cloud-based operations, overseas processors, or group company structures who need a complete, documented framework for every cross-border data transfer they make.
How it works
Step 1 — Read it. Every section exists for a reason, grounded in a specific regulatory obligation.
Step 2 — Understand it. Map the content against your current practices. Identify where you're strong and where gaps exist.
Step 3 — Make it yours. Tailor the language to reflect how your organisation actually operates. A policy that sounds like your firm is a policy your people will follow.
Step 4 — Take ownership. Assign clear accountability — Board approval, named SMF holder, designated policy owner. A policy without an owner is a liability, not an asset.
Step 5 — Operationalise it. Embed the policy into your governance calendar, training programme, and annual review cycle. This is where compliance becomes culture.
Or, get this free with RegTechPRO
Access this alongside the full compliance policy library — SM&CR, COBS, AML, Consumer Duty, GDPR, and more — for a fraction of the cost of consultancy.