Image 1 of 9
Image 1 of 9

 Image 2 of 9
Image 2 of 9
 Image 3 of 9
Image 3 of 9
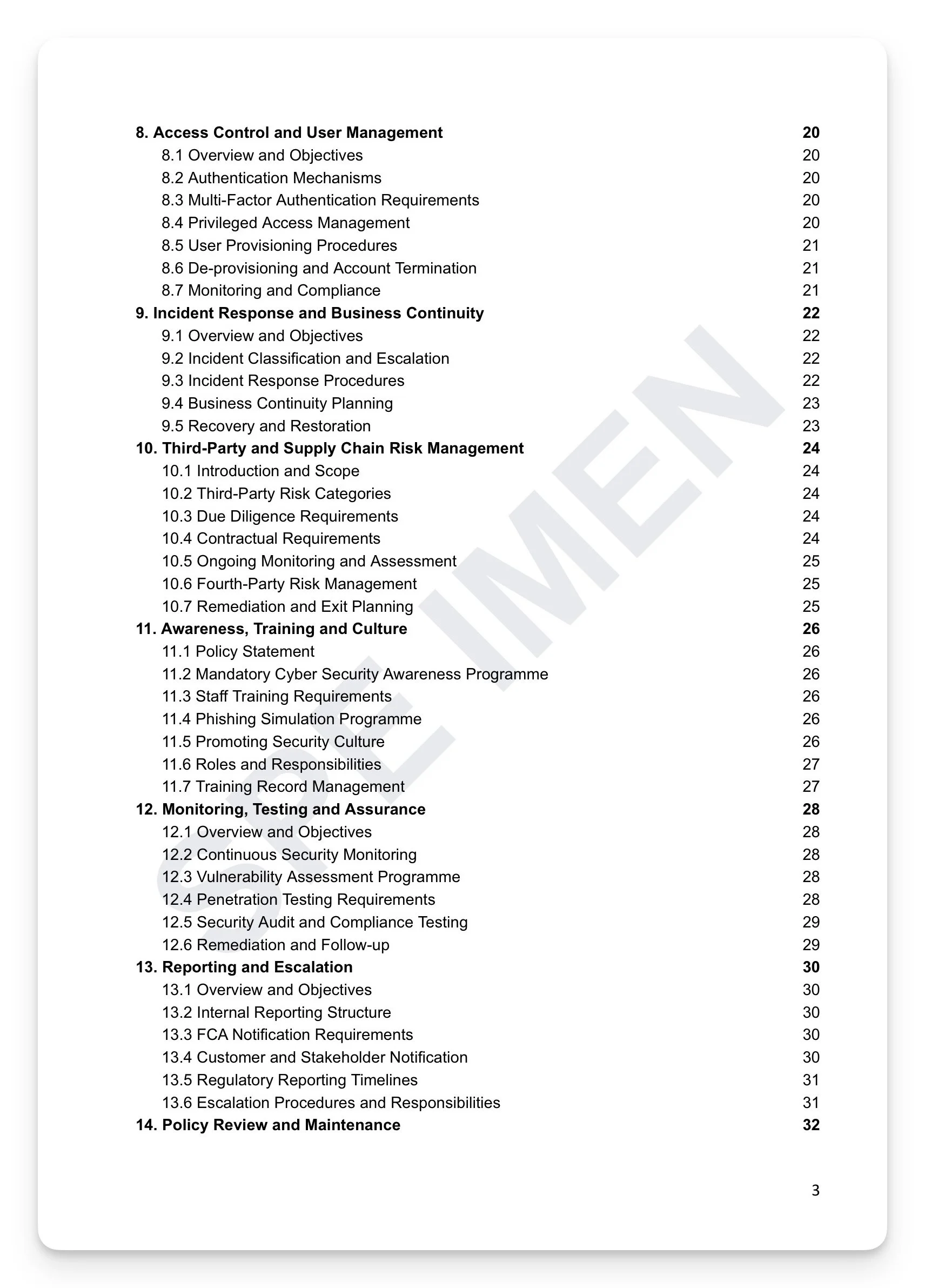
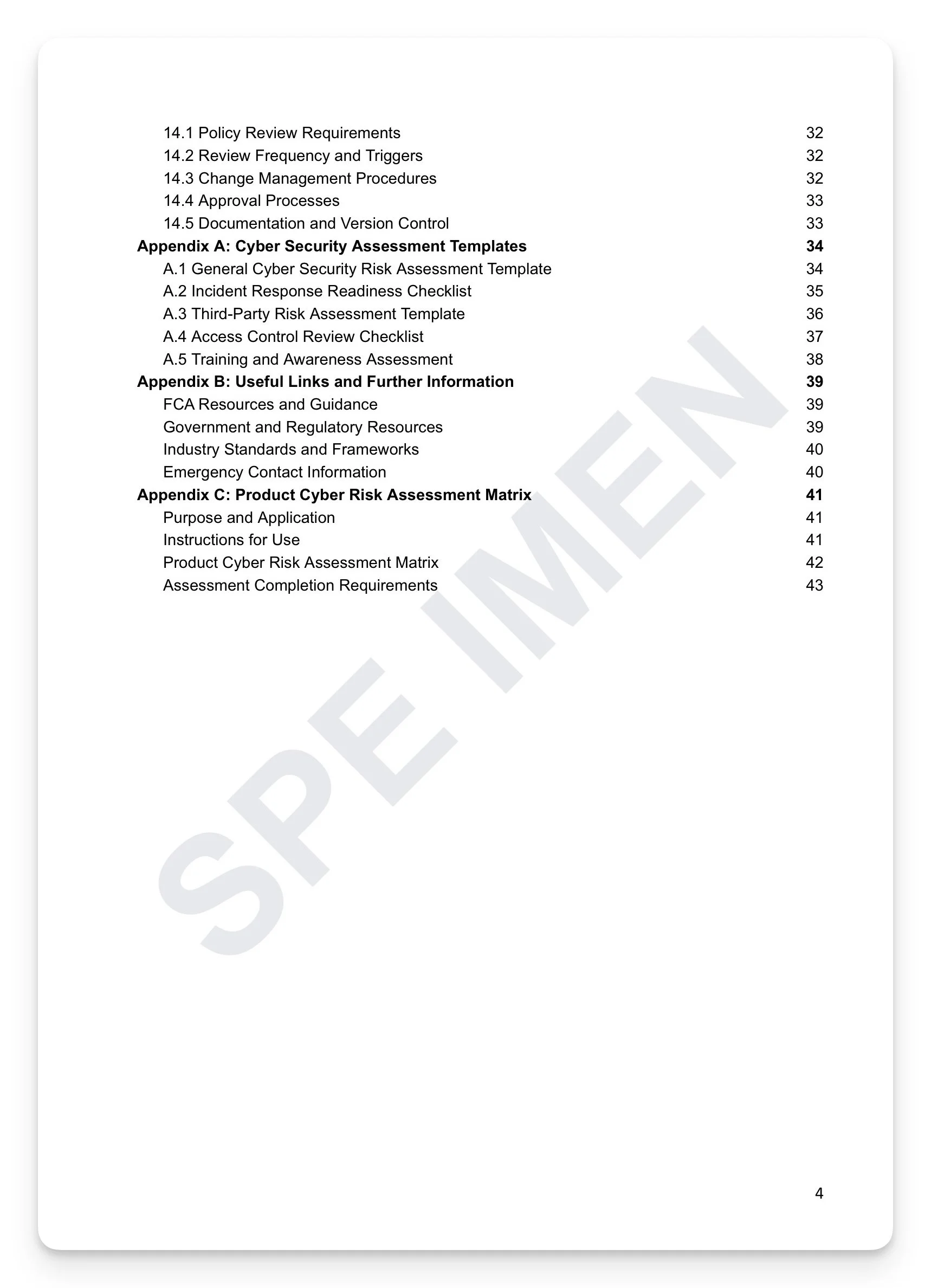 Image 4 of 9
Image 4 of 9
 Image 5 of 9
Image 5 of 9
 Image 6 of 9
Image 6 of 9
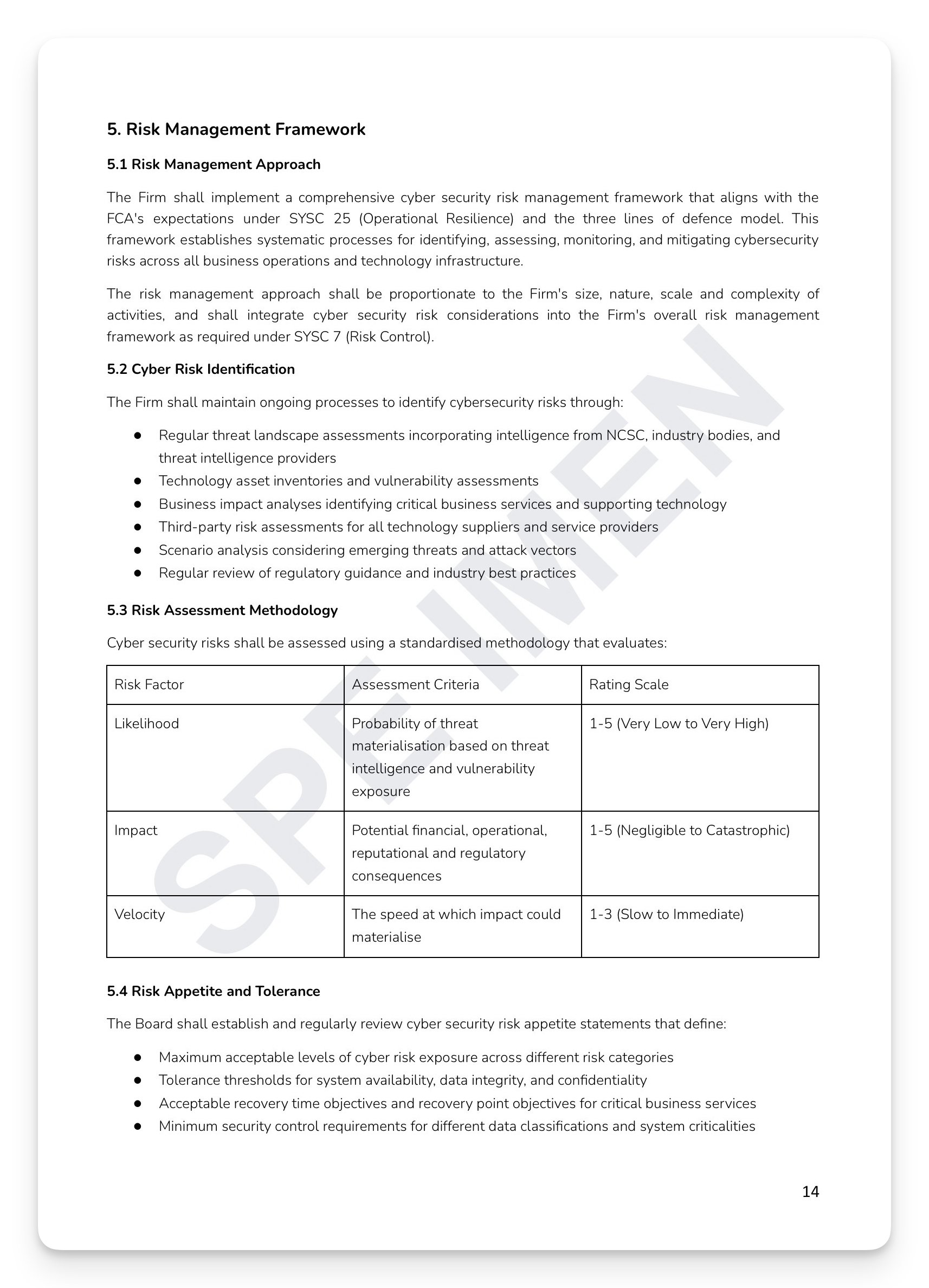 Image 7 of 9
Image 7 of 9
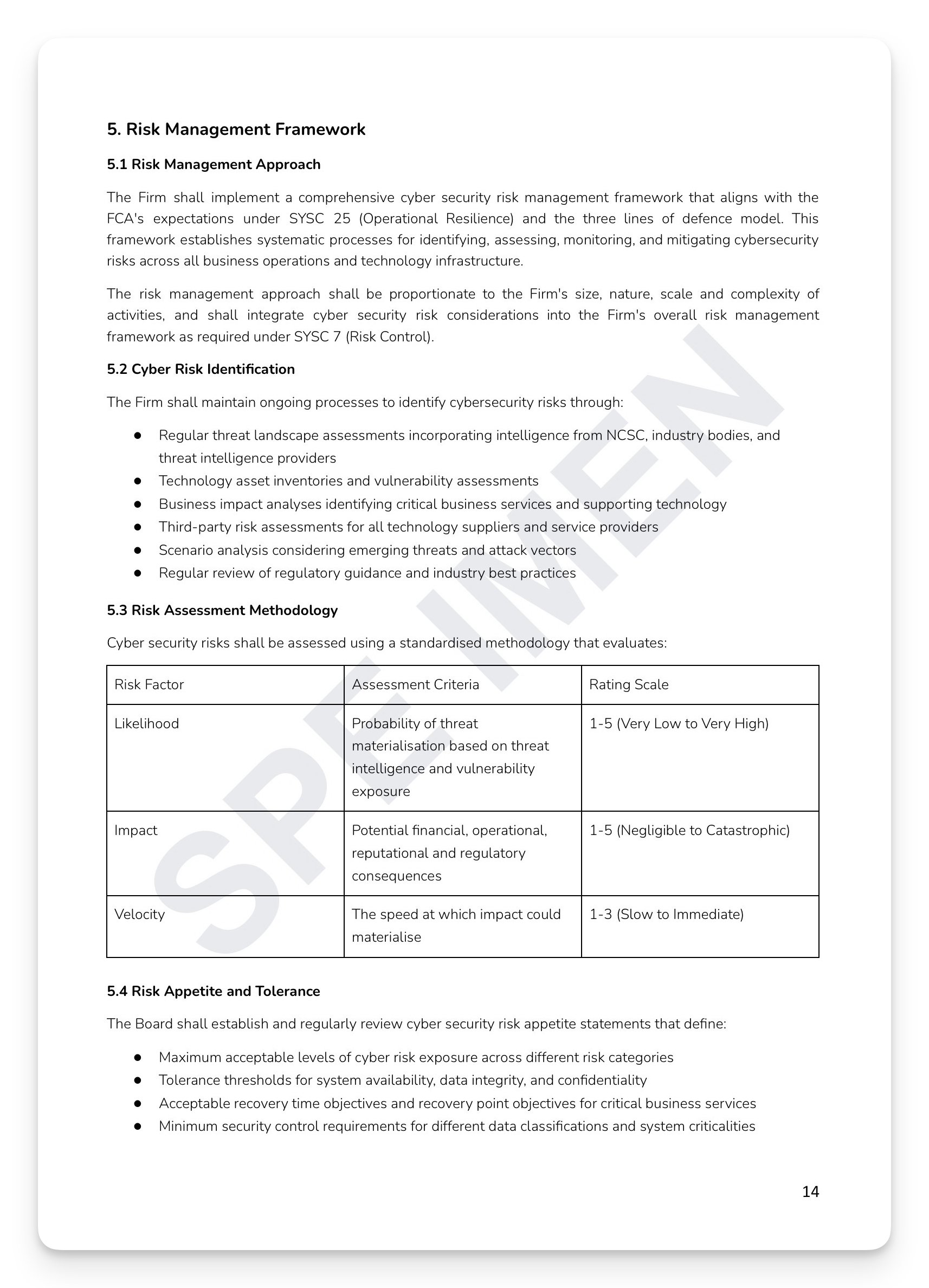
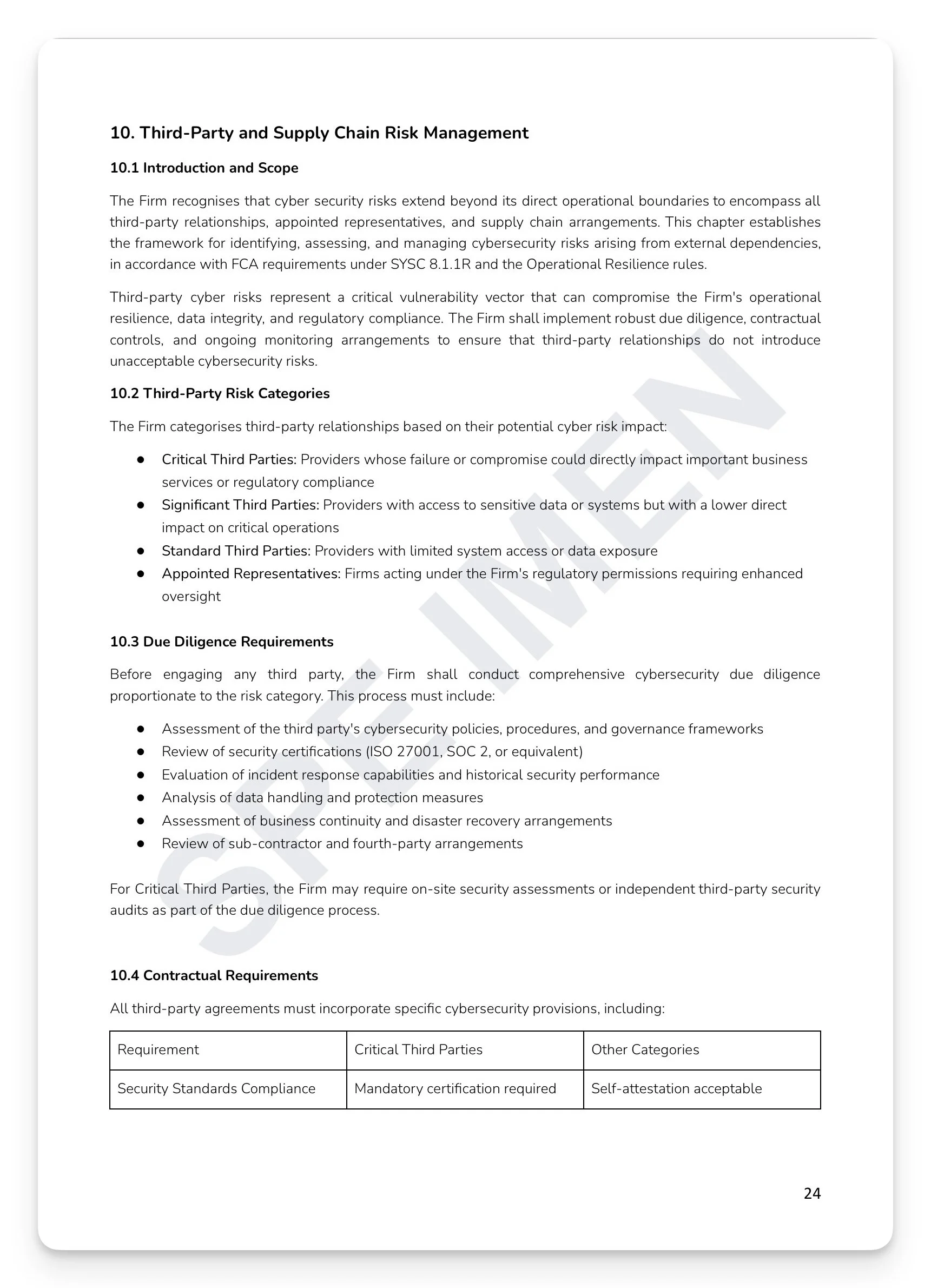 Image 8 of 9
Image 8 of 9
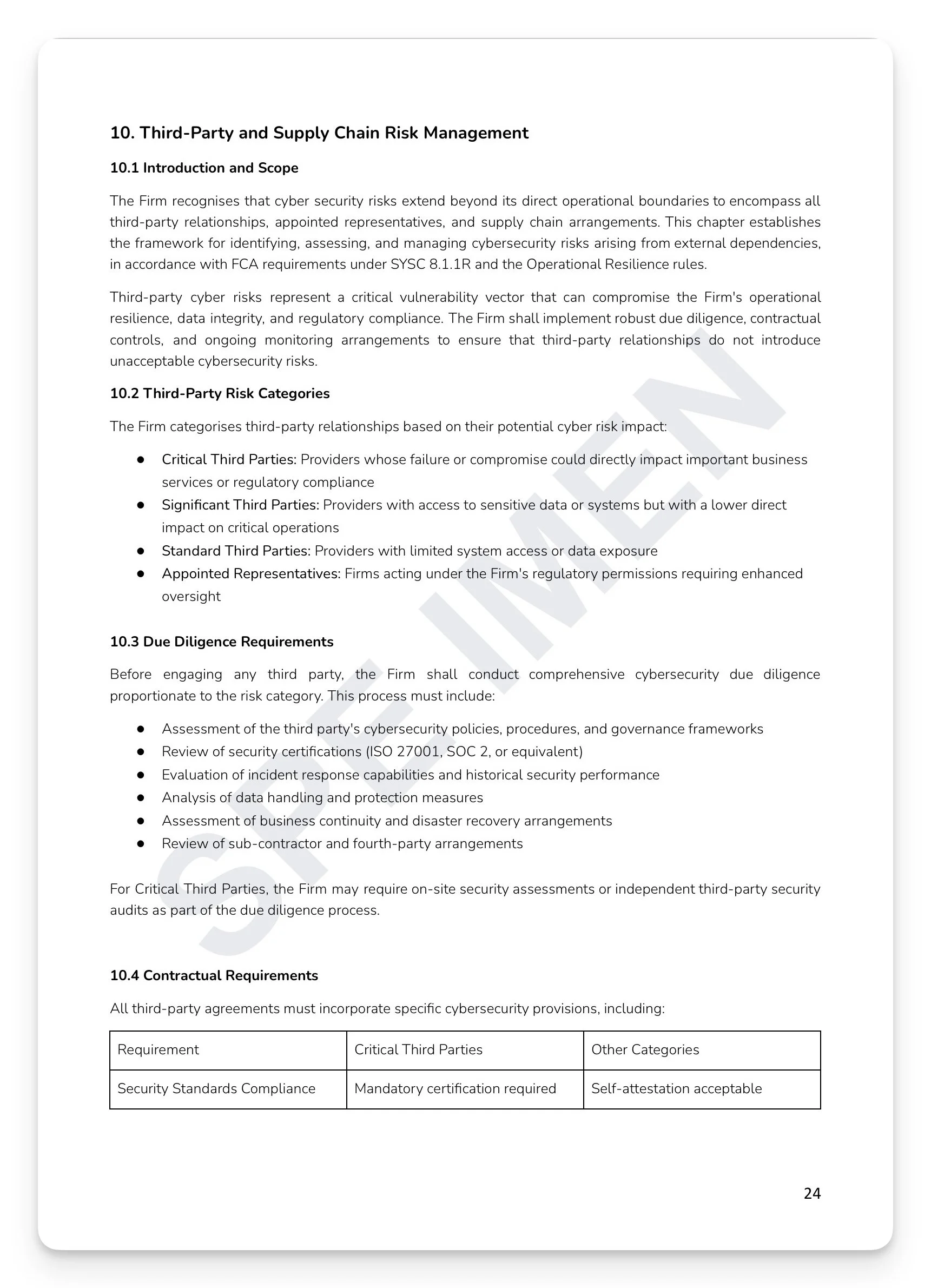
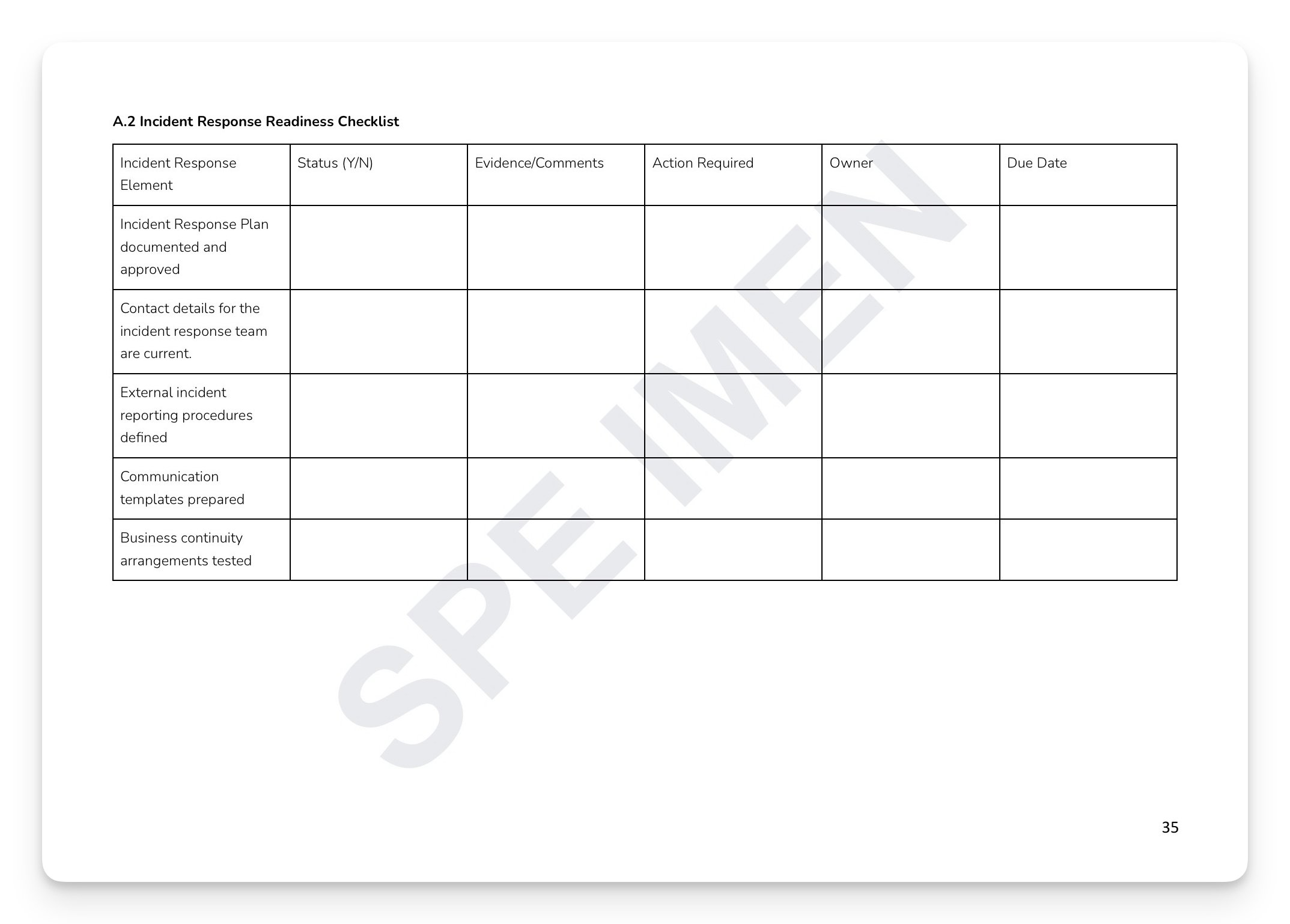 Image 9 of 9
Image 9 of 9

Cyber Security Risk Policy Template
Cyber attacks on UK financial services firms are increasing in frequency, sophistication, and regulatory consequence. Under SYSC 13, every FCA-regulated firm must have systems and controls to manage operational risk — and cyber security is now one of the FCA's highest supervisory priorities. The question the FCA asks isn't just what happened. It's whether the firm had a documented, tested, Board-approved framework before it did. The FCA doesn't wait.
What's included:
Risk management framework: cyber risk identification, risk assessment methodology, risk appetite, treatment, and monitoring
Secure configuration and system hardening: baseline configuration standards, vulnerability management, and patch management
Access control: MFA requirements, privileged access management, user provisioning, de-provisioning, and monitoring
Incident response and business continuity: classification, response procedures, BCP, and recovery and restoration
Third-party and supply chain risk: due diligence, contractual requirements, fourth-party risk management, and exit planning
Monitoring, testing, and assurance: continuous monitoring, vulnerability assessments, penetration testing, and compliance testing
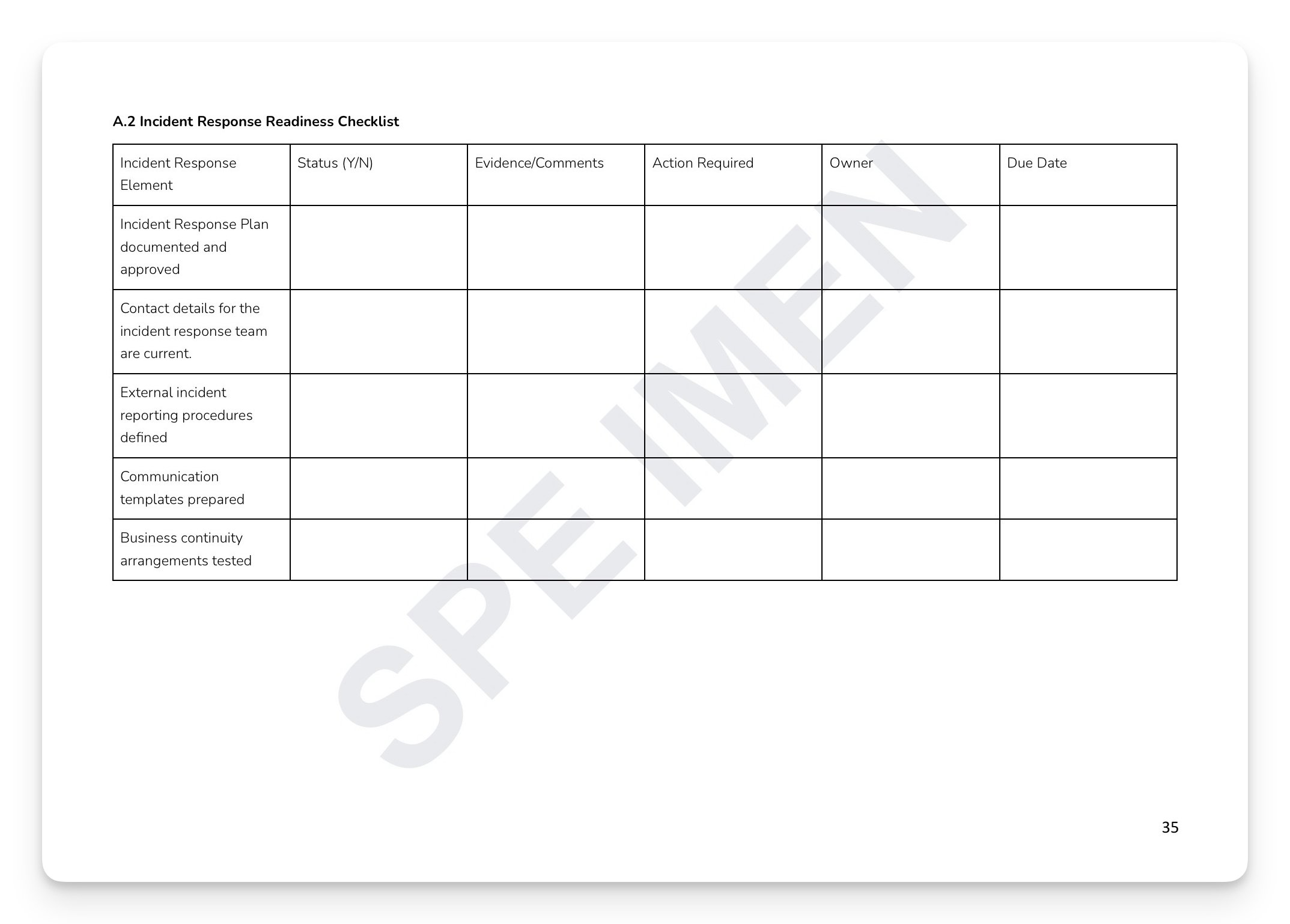
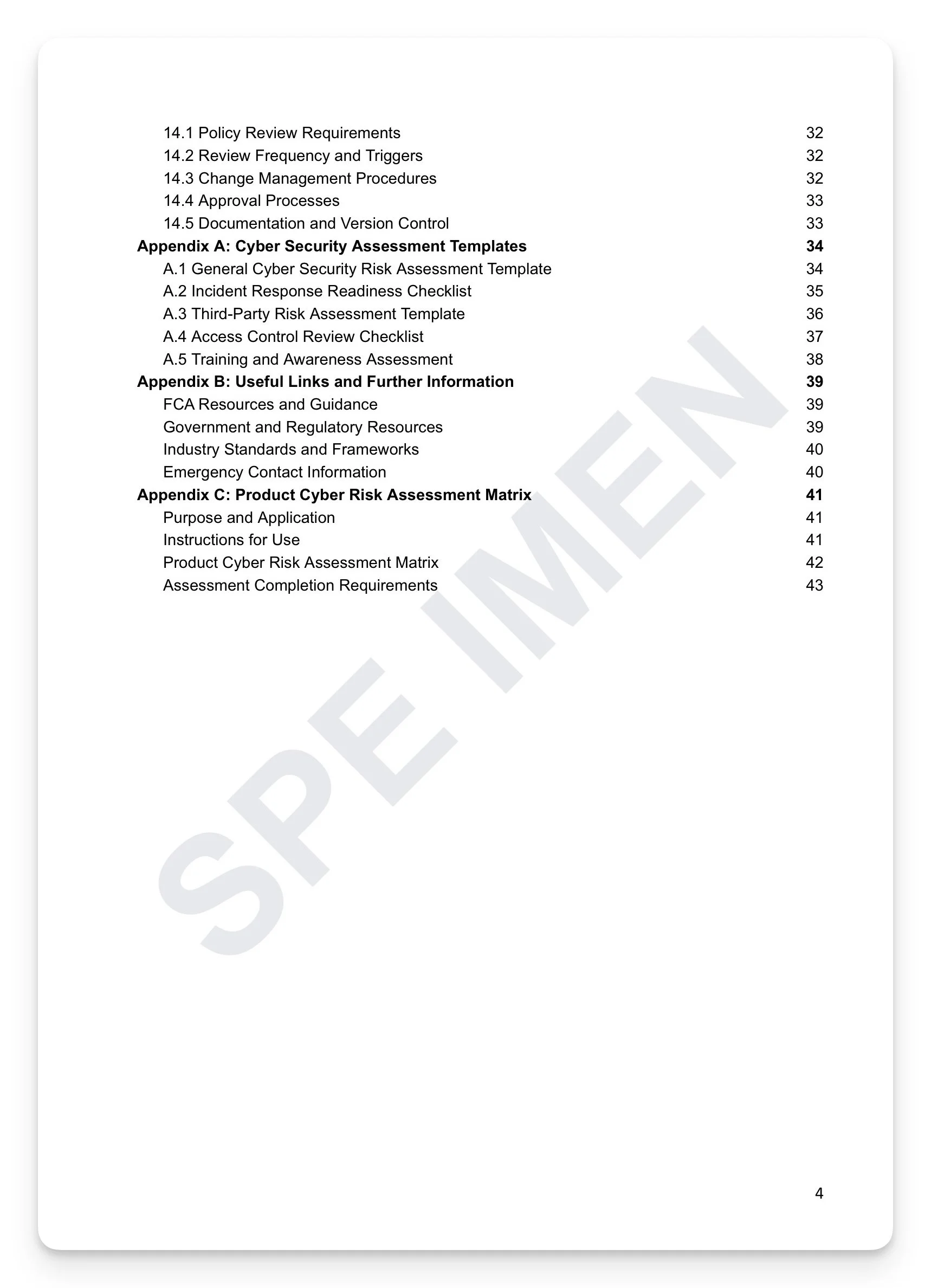
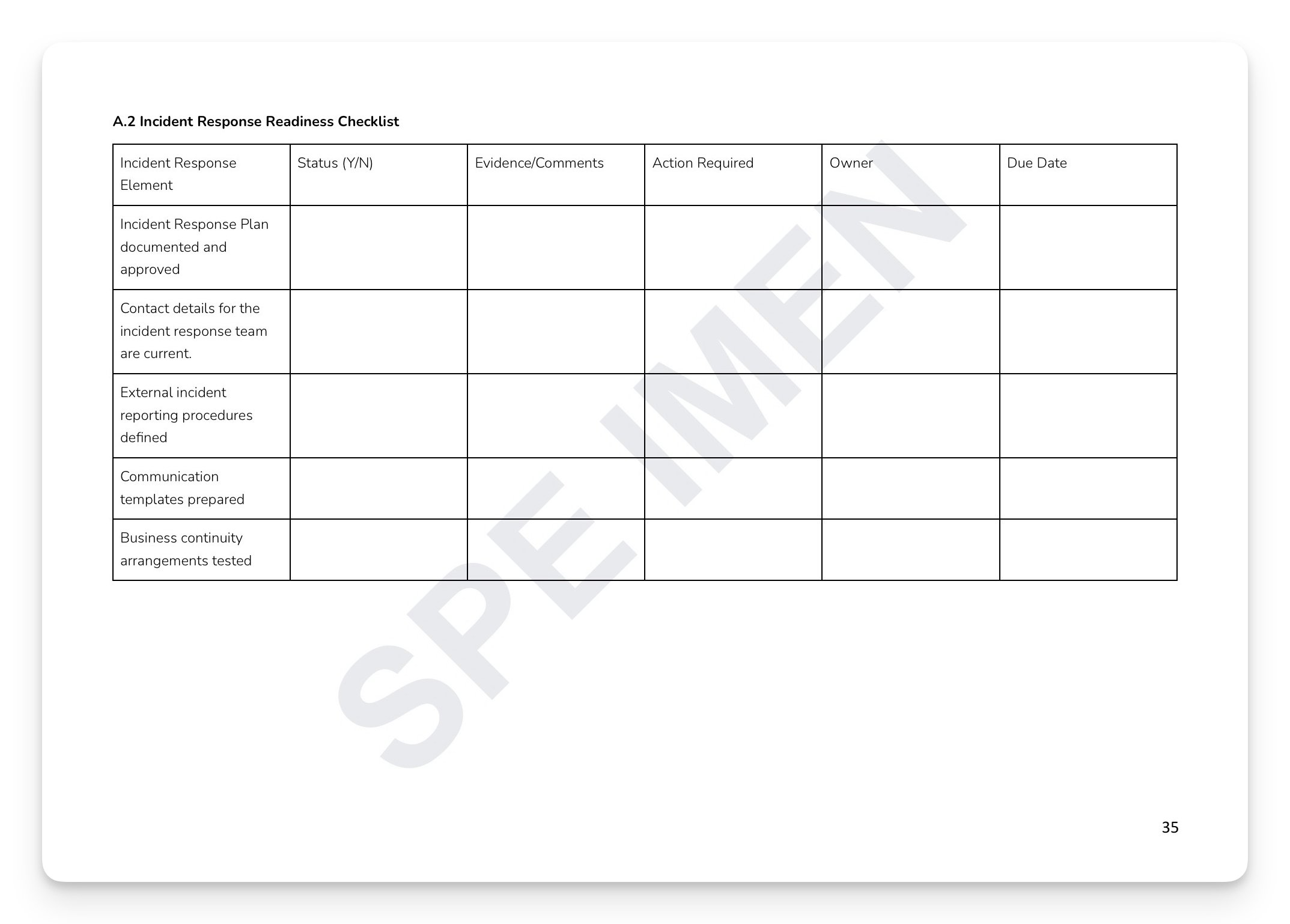
Ready-to-use appendices: Cyber Security Risk Assessment Template, Incident Response Readiness Checklist, Third-Party Risk Assessment Template, and Product Cyber Risk Assessment Matrix + much more
Who is this for?
Compliance Officers, Chief Risk Officers, IT Security Managers, SMF holders, and Boards at FCA-regulated firms.
How it works
Step 1 — Read it. Every section exists for a reason, grounded in a specific regulatory obligation.
Step 2 — Understand it. Map the content against your current practices. Identify where you're strong and where gaps exist.
Step 3 — Make it yours. Tailor the language to reflect how your organisation actually operates. A policy that sounds like your firm is a policy your people will follow.
Step 4 — Take ownership. Assign clear accountability — Board approval, named SMF holder, designated policy owner. A policy without an owner is a liability, not an asset.
Step 5 — Operationalise it. Embed the policy into your governance calendar, training programme, and annual review cycle. This is where compliance becomes culture.
Or, get this free with RegTechPRO
Access this alongside the full compliance policy library — SM&CR, COBS, AML, Consumer Duty, GDPR, and more — for a fraction of the cost of consultancy.
Cyber attacks on UK financial services firms are increasing in frequency, sophistication, and regulatory consequence. Under SYSC 13, every FCA-regulated firm must have systems and controls to manage operational risk — and cyber security is now one of the FCA's highest supervisory priorities. The question the FCA asks isn't just what happened. It's whether the firm had a documented, tested, Board-approved framework before it did. The FCA doesn't wait.
What's included:
Risk management framework: cyber risk identification, risk assessment methodology, risk appetite, treatment, and monitoring
Secure configuration and system hardening: baseline configuration standards, vulnerability management, and patch management
Access control: MFA requirements, privileged access management, user provisioning, de-provisioning, and monitoring
Incident response and business continuity: classification, response procedures, BCP, and recovery and restoration
Third-party and supply chain risk: due diligence, contractual requirements, fourth-party risk management, and exit planning
Monitoring, testing, and assurance: continuous monitoring, vulnerability assessments, penetration testing, and compliance testing
Ready-to-use appendices: Cyber Security Risk Assessment Template, Incident Response Readiness Checklist, Third-Party Risk Assessment Template, and Product Cyber Risk Assessment Matrix + much more
Who is this for?
Compliance Officers, Chief Risk Officers, IT Security Managers, SMF holders, and Boards at FCA-regulated firms.
How it works
Step 1 — Read it. Every section exists for a reason, grounded in a specific regulatory obligation.
Step 2 — Understand it. Map the content against your current practices. Identify where you're strong and where gaps exist.
Step 3 — Make it yours. Tailor the language to reflect how your organisation actually operates. A policy that sounds like your firm is a policy your people will follow.
Step 4 — Take ownership. Assign clear accountability — Board approval, named SMF holder, designated policy owner. A policy without an owner is a liability, not an asset.
Step 5 — Operationalise it. Embed the policy into your governance calendar, training programme, and annual review cycle. This is where compliance becomes culture.
Or, get this free with RegTechPRO
Access this alongside the full compliance policy library — SM&CR, COBS, AML, Consumer Duty, GDPR, and more — for a fraction of the cost of consultancy.