 Image 1 of 7
Image 1 of 7
 Image 2 of 7
Image 2 of 7
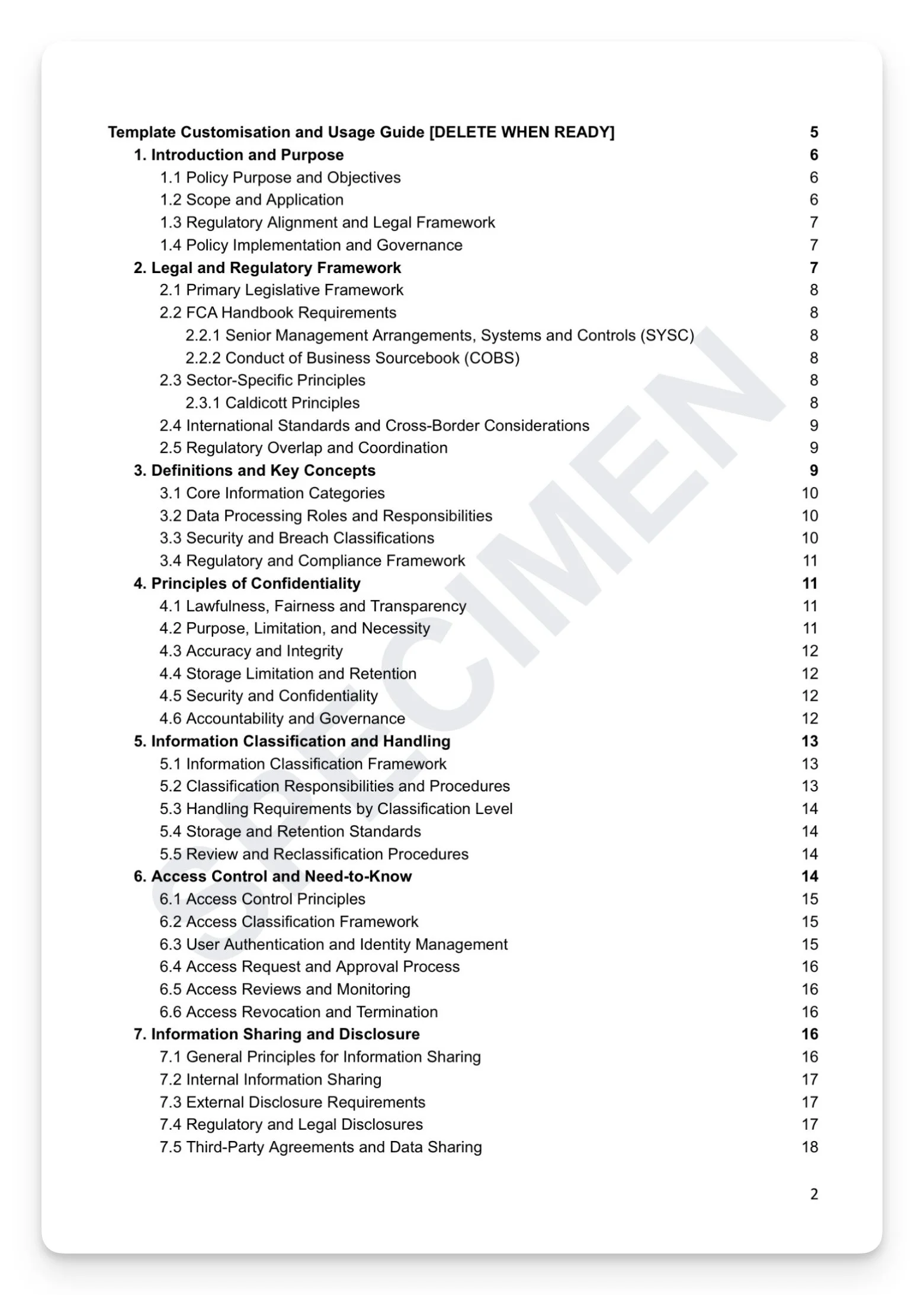
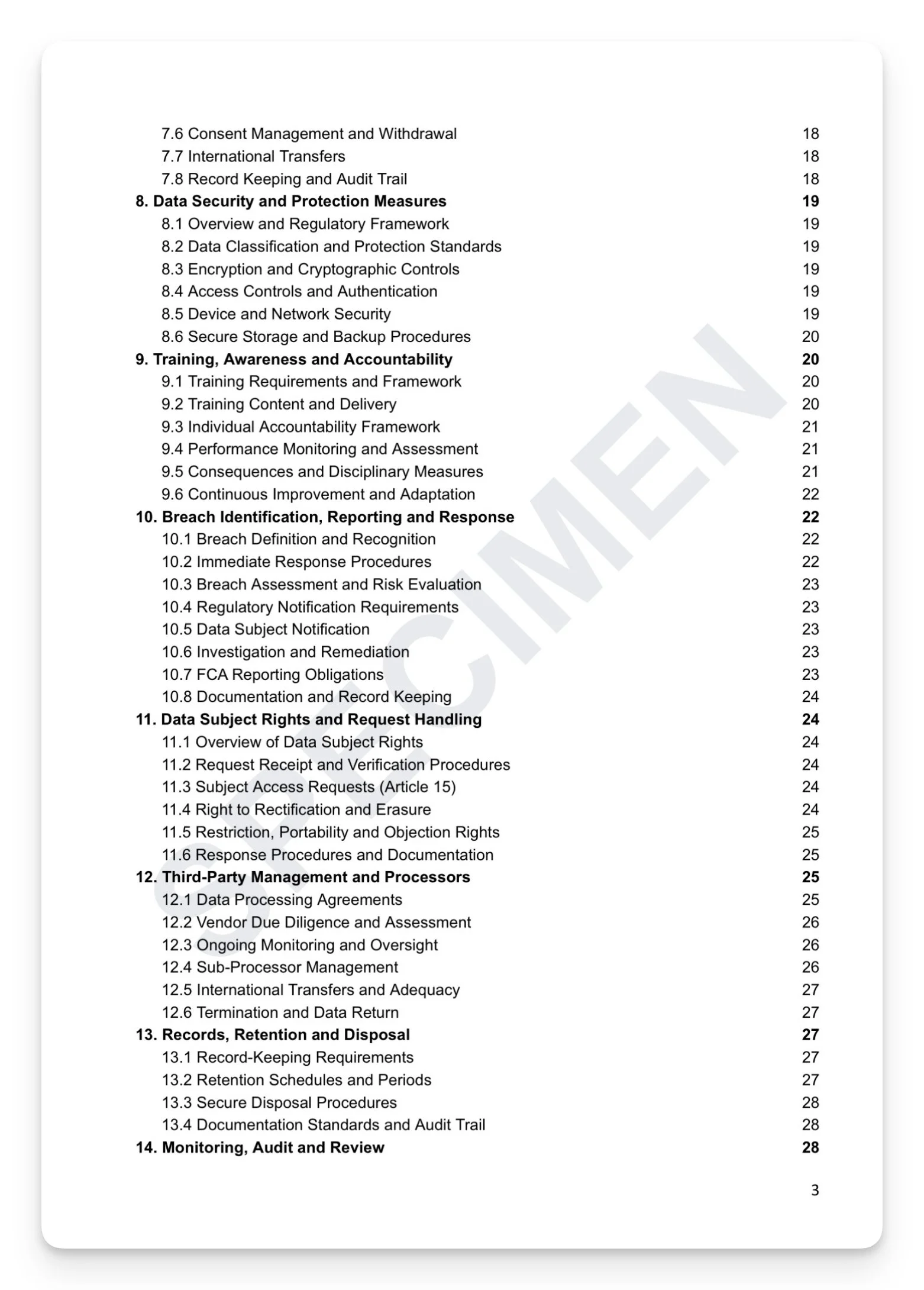 Image 3 of 7
Image 3 of 7
 Image 4 of 7
Image 4 of 7
 Image 5 of 7
Image 5 of 7
 Image 6 of 7
Image 6 of 7
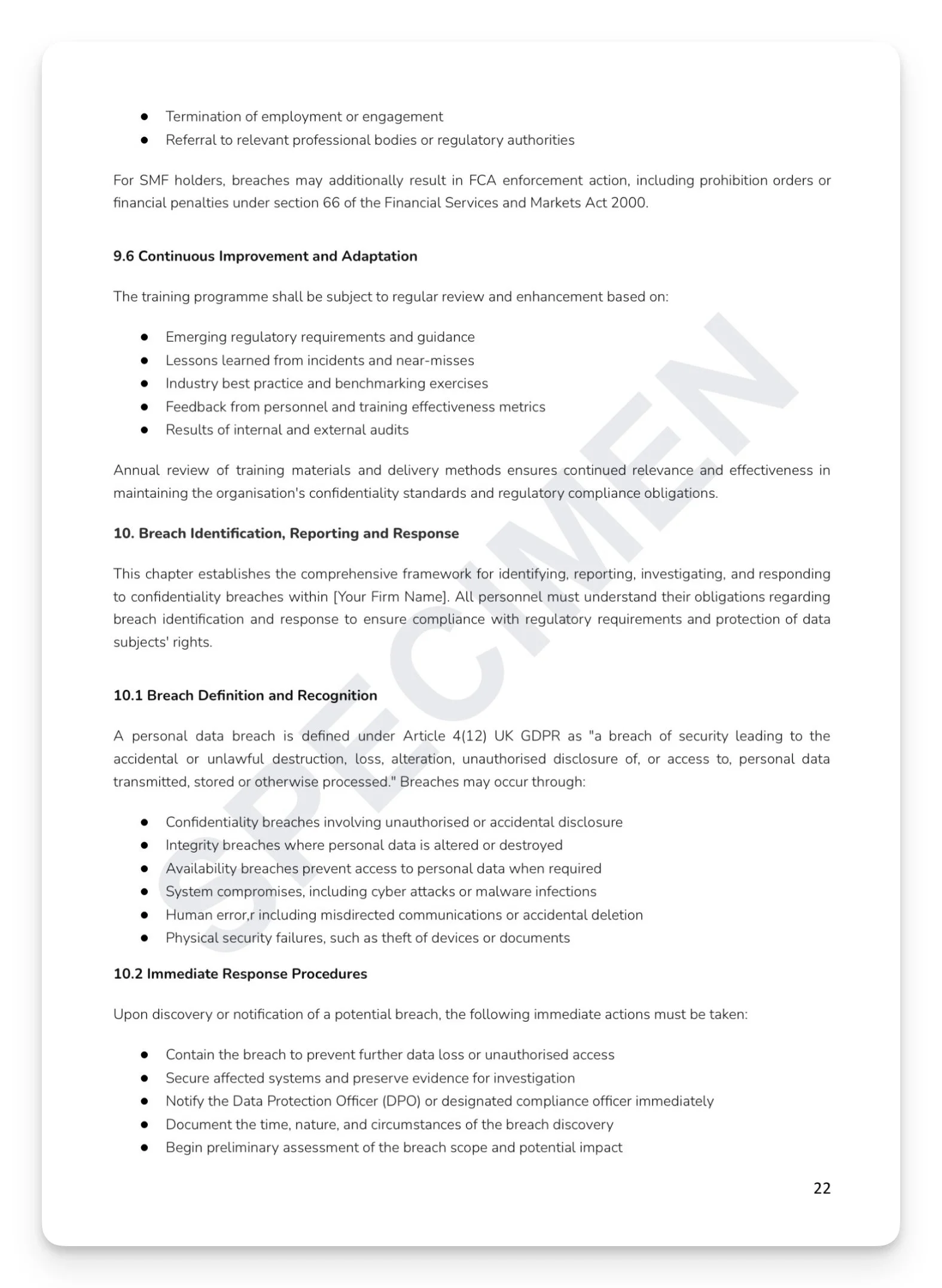
 Image 7 of 7
Image 7 of 7
Confidentiality Policy Template
Confidentiality isn't just a professional obligation — it's a regulatory one. A confidentiality failure is simultaneously a data protection breach, a potential conduct violation, and evidence of inadequate systems and controls. The consequences span ICO enforcement, FCA supervisory action, and civil liability to affected clients. Most firms have a confidentiality clause in their employment contracts. Few have a complete governance framework. The FCA doesn't wait.
What's included:
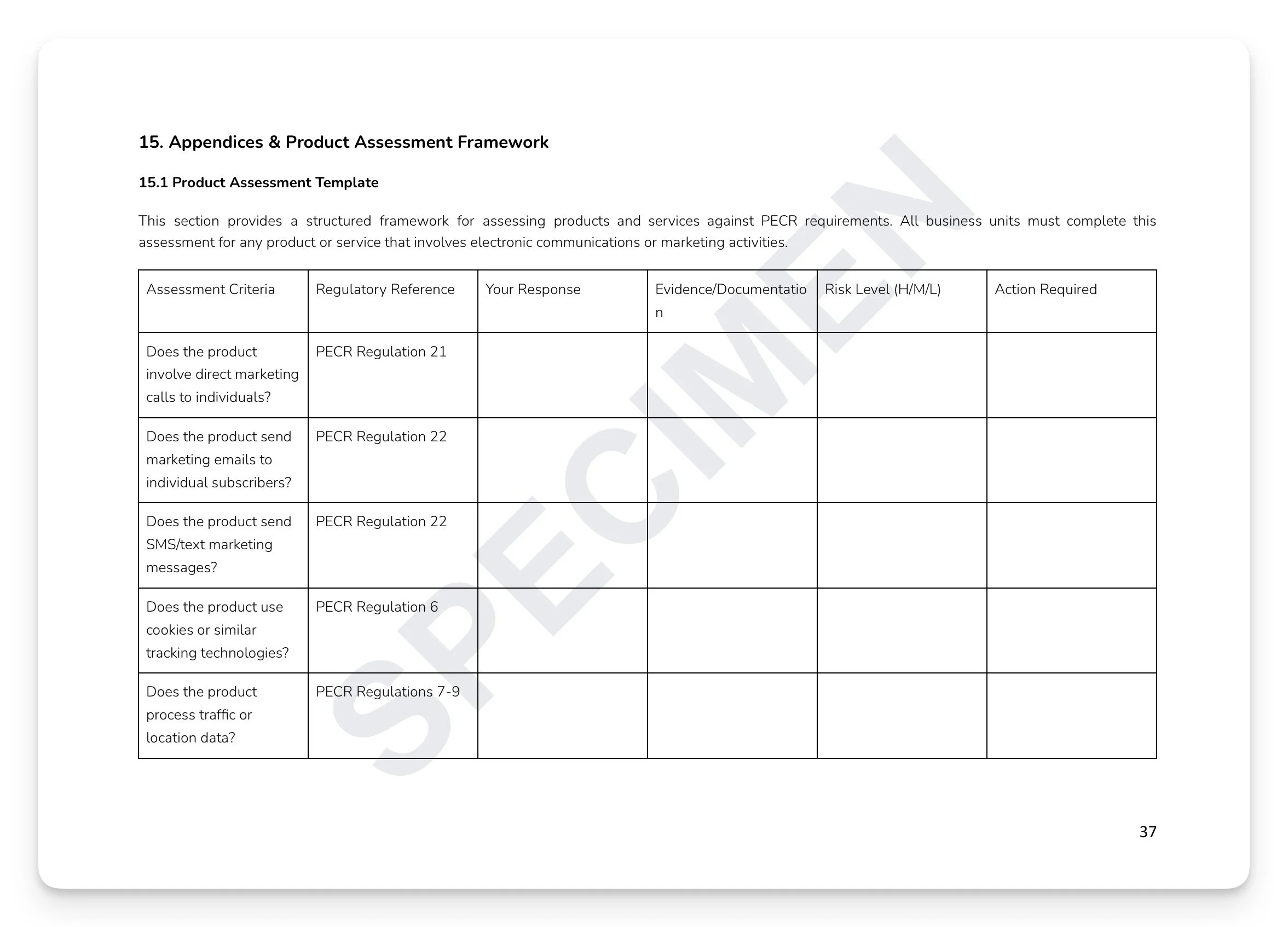
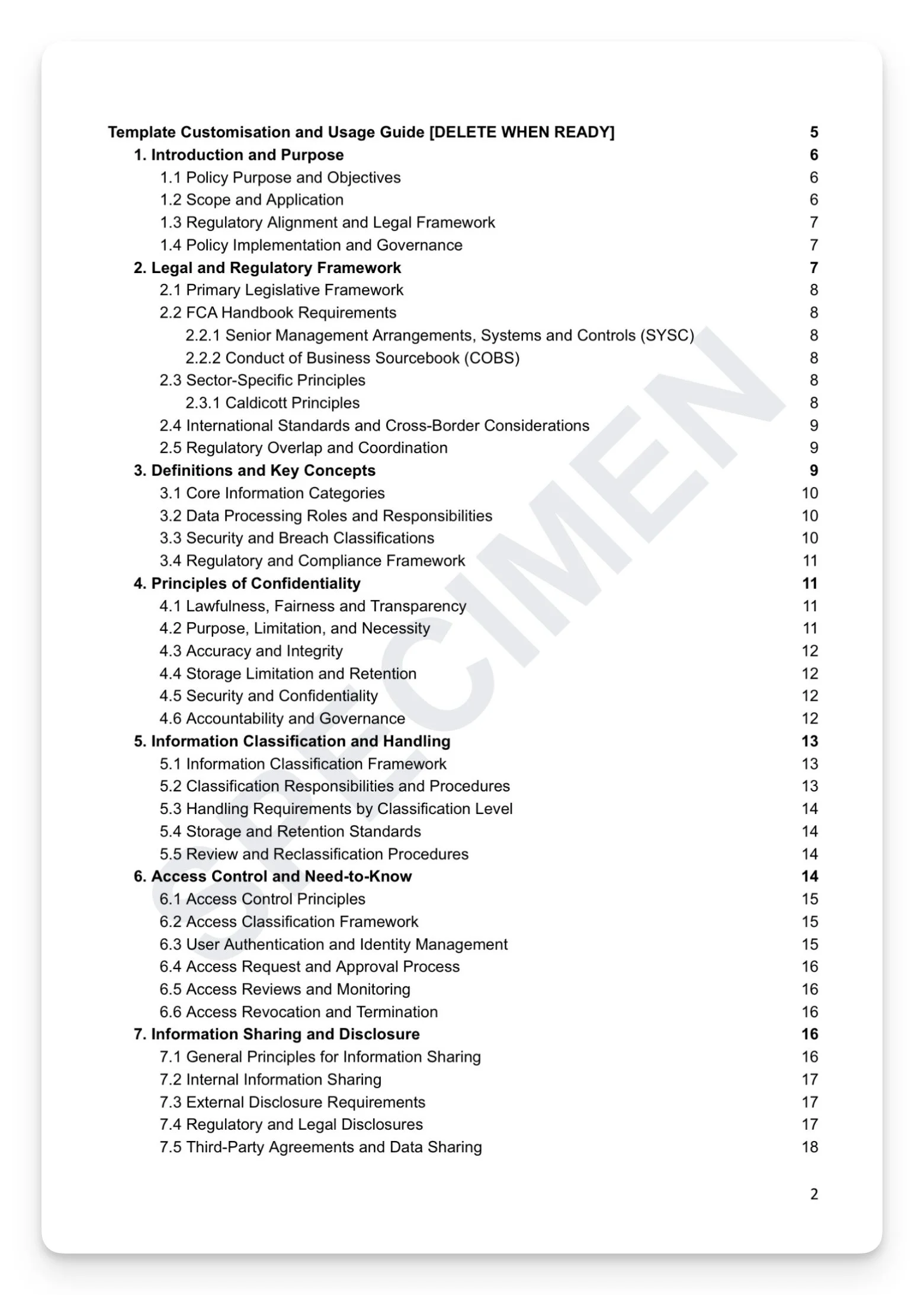
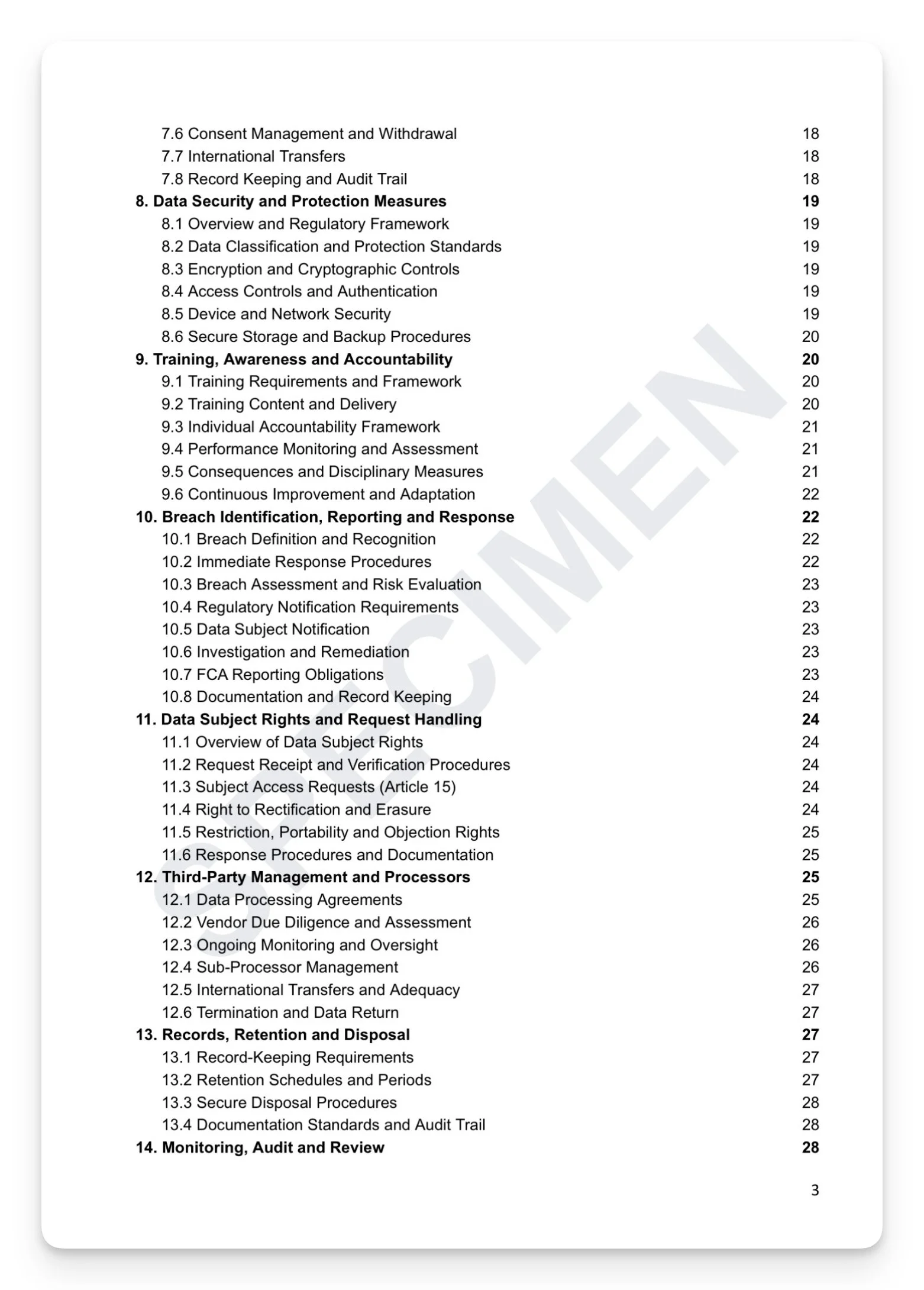
Information classification and handling: classification framework, handling requirements by level, storage standards, and reclassification procedures
Access control and need-to-know: user authentication, identity management, access request and approval, reviews, and revocation
Data security: encryption and cryptographic controls, device and network security, and secure storage and backup
Breach response: ICO 72-hour notification, FCA reporting obligations, data subject notification, and investigation and remediation
Data subject rights: Articles 15–22 with response procedures and documentation requirements
Third-party management: vendor due diligence, data processing agreements, sub-processor management, and international transfers
Ready-to-use appendices: Internal Breach Notification Form, Regulatory Notification Template, Processor Agreement Checklist, and Confidentiality Assessment Matrix
+ much more
Who is this for?
Data Protection Officers, Compliance Officers, senior management, IT security teams, and HR functions at FCA-regulated firms.
How it works
Step 1 — Read it. Every section exists for a reason, grounded in a specific regulatory obligation.
Step 2 — Understand it. Map the content against your current practices. Identify where you're strong and where gaps exist.
Step 3 — Make it yours. Tailor the language to reflect how your organisation actually operates. A policy that sounds like your firm is a policy your people will follow.
Step 4 — Take ownership. Assign clear accountability — Board approval, named SMF holder, designated policy owner. A policy without an owner is a liability, not an asset.
Step 5 — Operationalise it. Embed the policy into your governance calendar, training programme, and annual review cycle. This is where compliance becomes culture.
Or, get this free with RegTechPRO
Access this alongside the full compliance policy library — SM&CR, COBS, AML, Consumer Duty, GDPR, and more — for a fraction of the cost of consultancy.
Confidentiality isn't just a professional obligation — it's a regulatory one. A confidentiality failure is simultaneously a data protection breach, a potential conduct violation, and evidence of inadequate systems and controls. The consequences span ICO enforcement, FCA supervisory action, and civil liability to affected clients. Most firms have a confidentiality clause in their employment contracts. Few have a complete governance framework. The FCA doesn't wait.
What's included:
Information classification and handling: classification framework, handling requirements by level, storage standards, and reclassification procedures
Access control and need-to-know: user authentication, identity management, access request and approval, reviews, and revocation
Data security: encryption and cryptographic controls, device and network security, and secure storage and backup
Breach response: ICO 72-hour notification, FCA reporting obligations, data subject notification, and investigation and remediation
Data subject rights: Articles 15–22 with response procedures and documentation requirements
Third-party management: vendor due diligence, data processing agreements, sub-processor management, and international transfers
Ready-to-use appendices: Internal Breach Notification Form, Regulatory Notification Template, Processor Agreement Checklist, and Confidentiality Assessment Matrix
+ much more
Who is this for?
Data Protection Officers, Compliance Officers, senior management, IT security teams, and HR functions at FCA-regulated firms.
How it works
Step 1 — Read it. Every section exists for a reason, grounded in a specific regulatory obligation.
Step 2 — Understand it. Map the content against your current practices. Identify where you're strong and where gaps exist.
Step 3 — Make it yours. Tailor the language to reflect how your organisation actually operates. A policy that sounds like your firm is a policy your people will follow.
Step 4 — Take ownership. Assign clear accountability — Board approval, named SMF holder, designated policy owner. A policy without an owner is a liability, not an asset.
Step 5 — Operationalise it. Embed the policy into your governance calendar, training programme, and annual review cycle. This is where compliance becomes culture.
Or, get this free with RegTechPRO
Access this alongside the full compliance policy library — SM&CR, COBS, AML, Consumer Duty, GDPR, and more — for a fraction of the cost of consultancy.