Image 1 of 7
Image 1 of 7

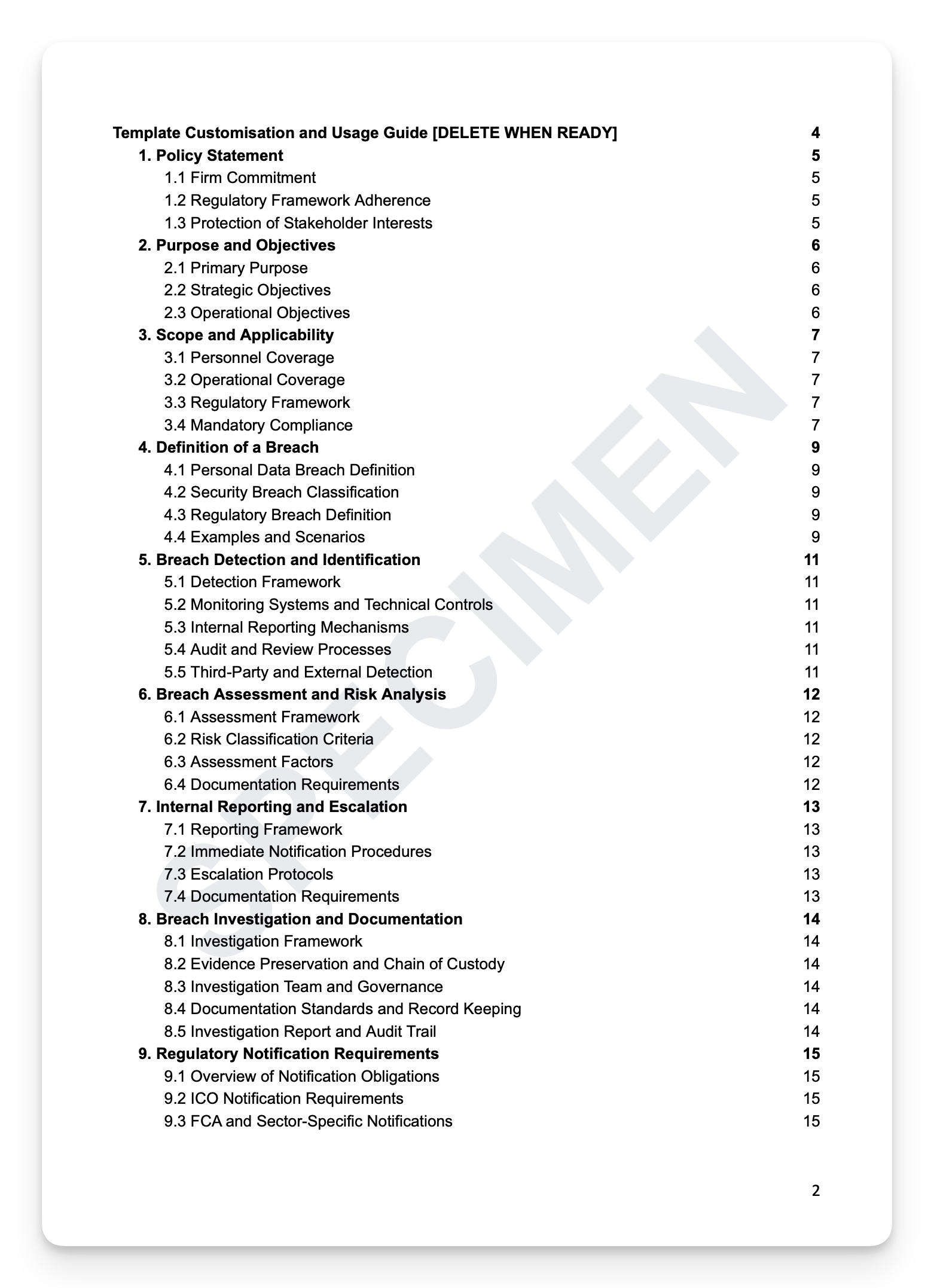 Image 2 of 7
Image 2 of 7
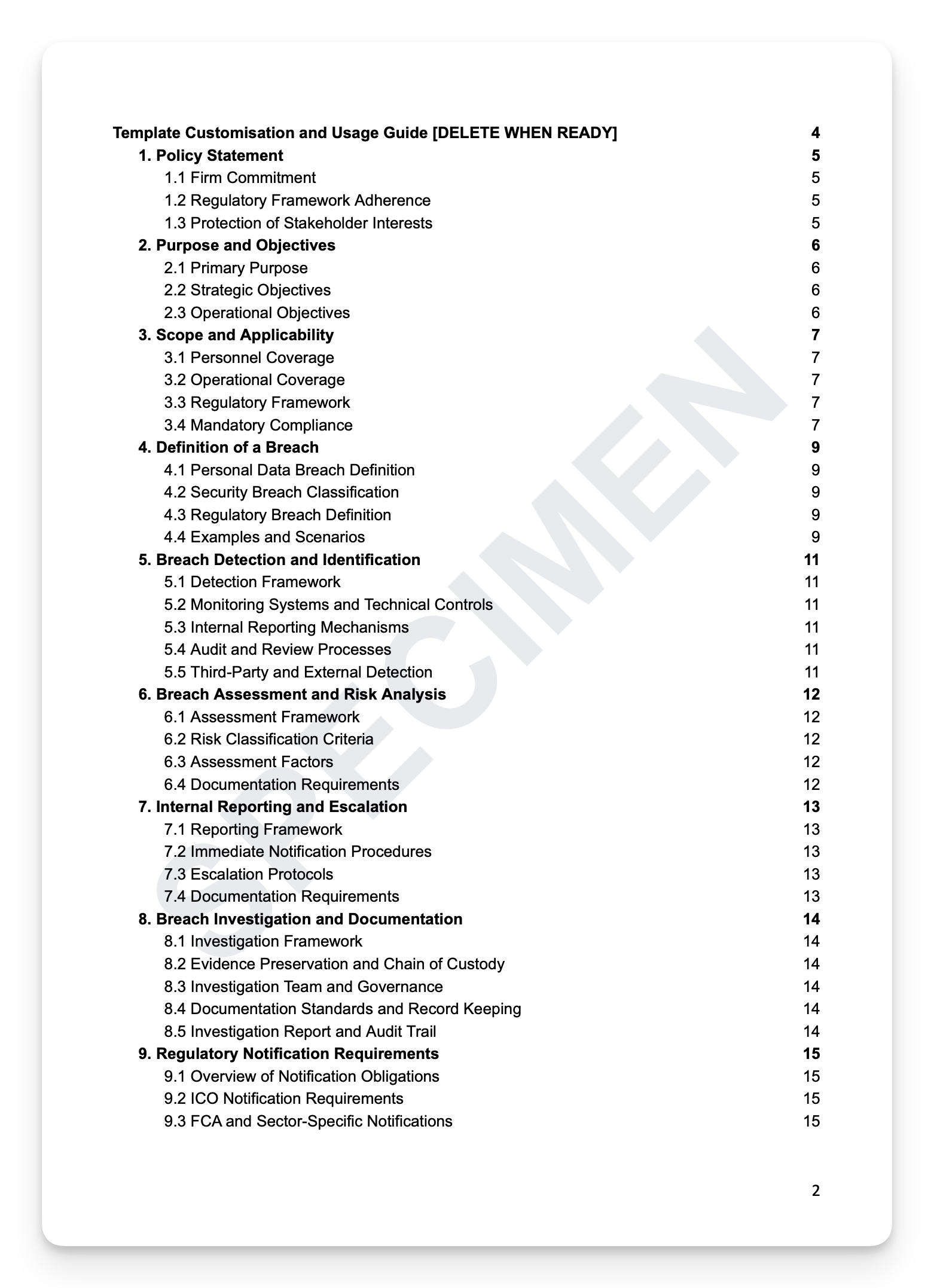
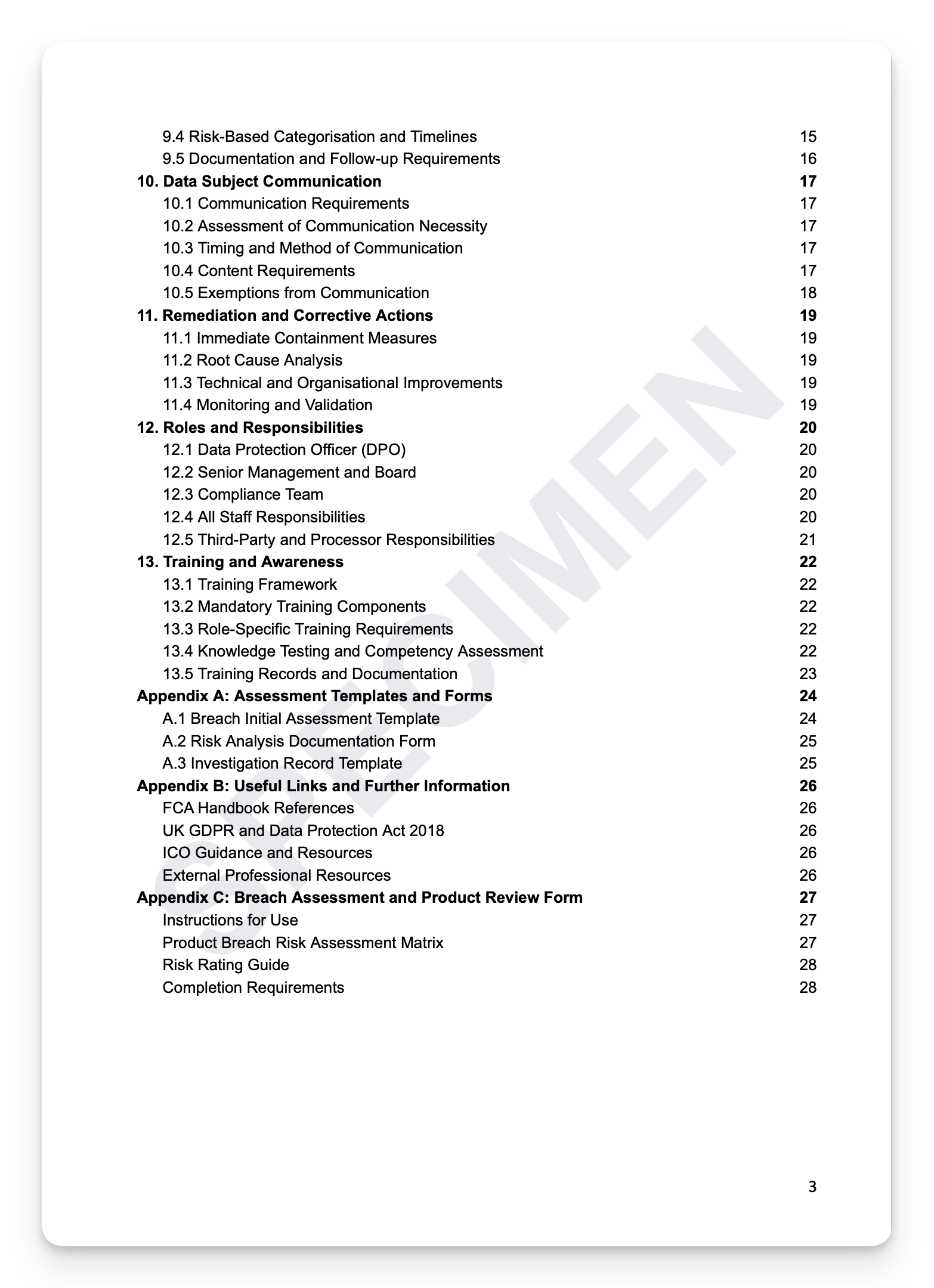 Image 3 of 7
Image 3 of 7
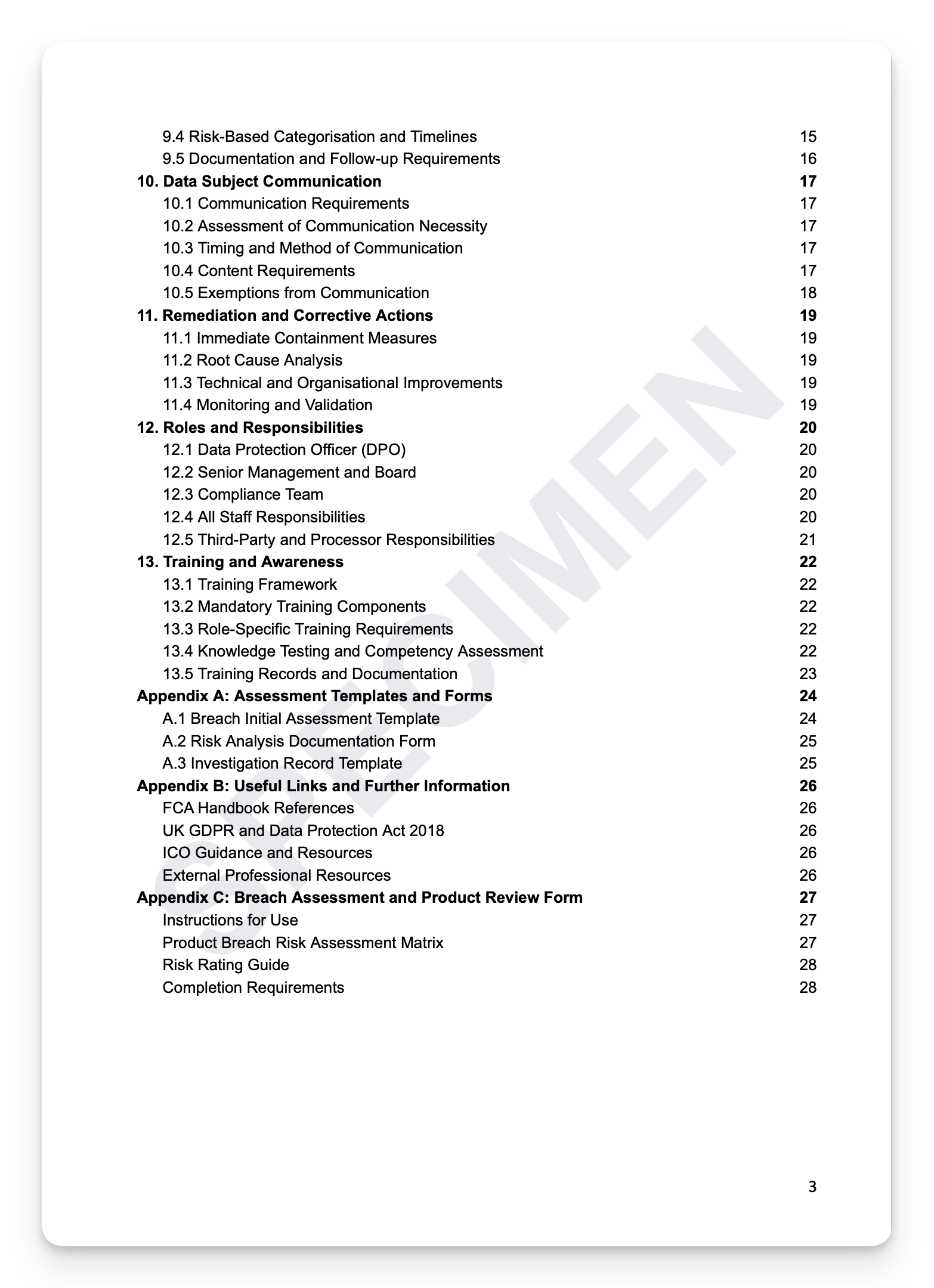
 Image 4 of 7
Image 4 of 7
 Image 5 of 7
Image 5 of 7
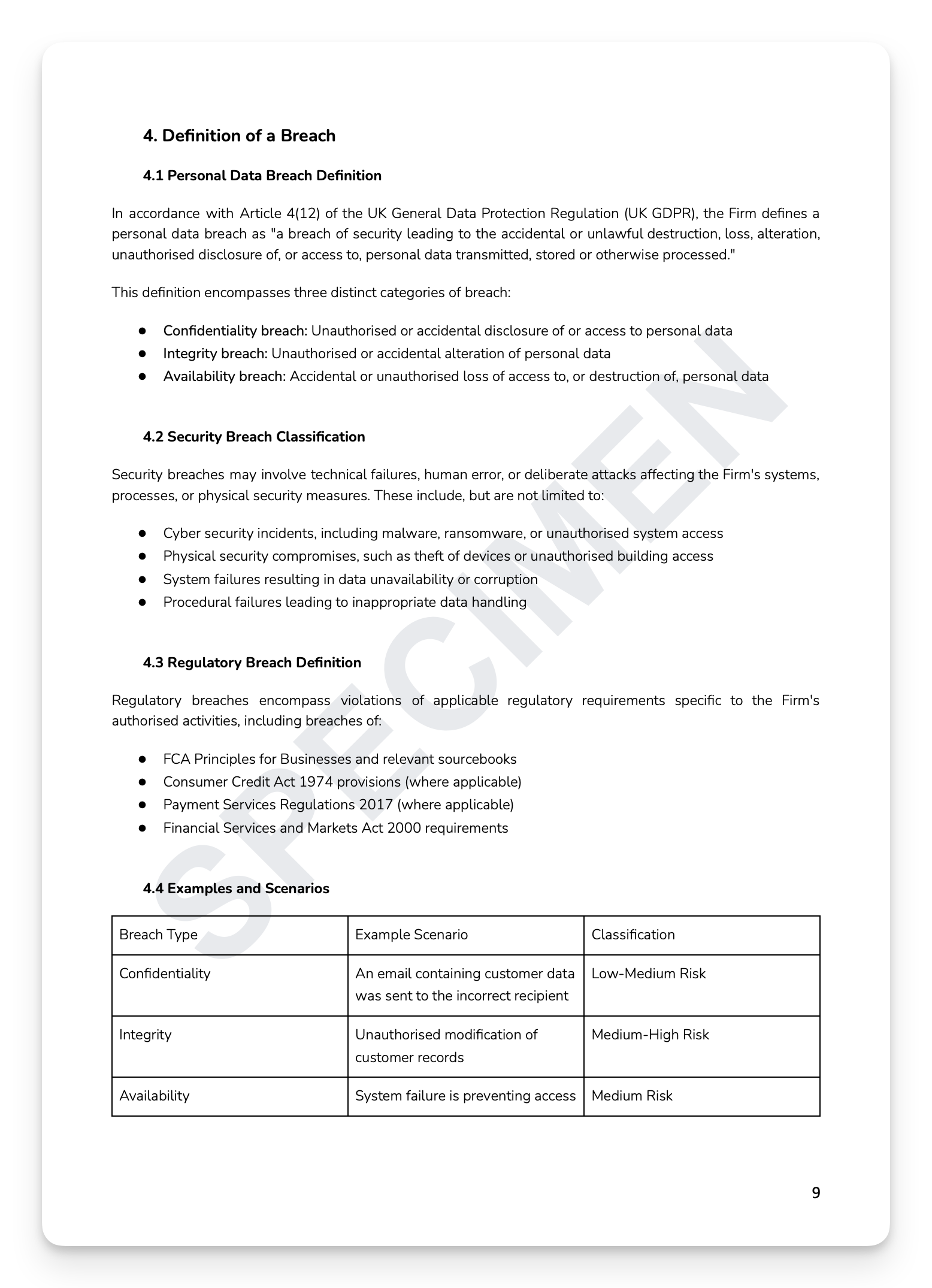
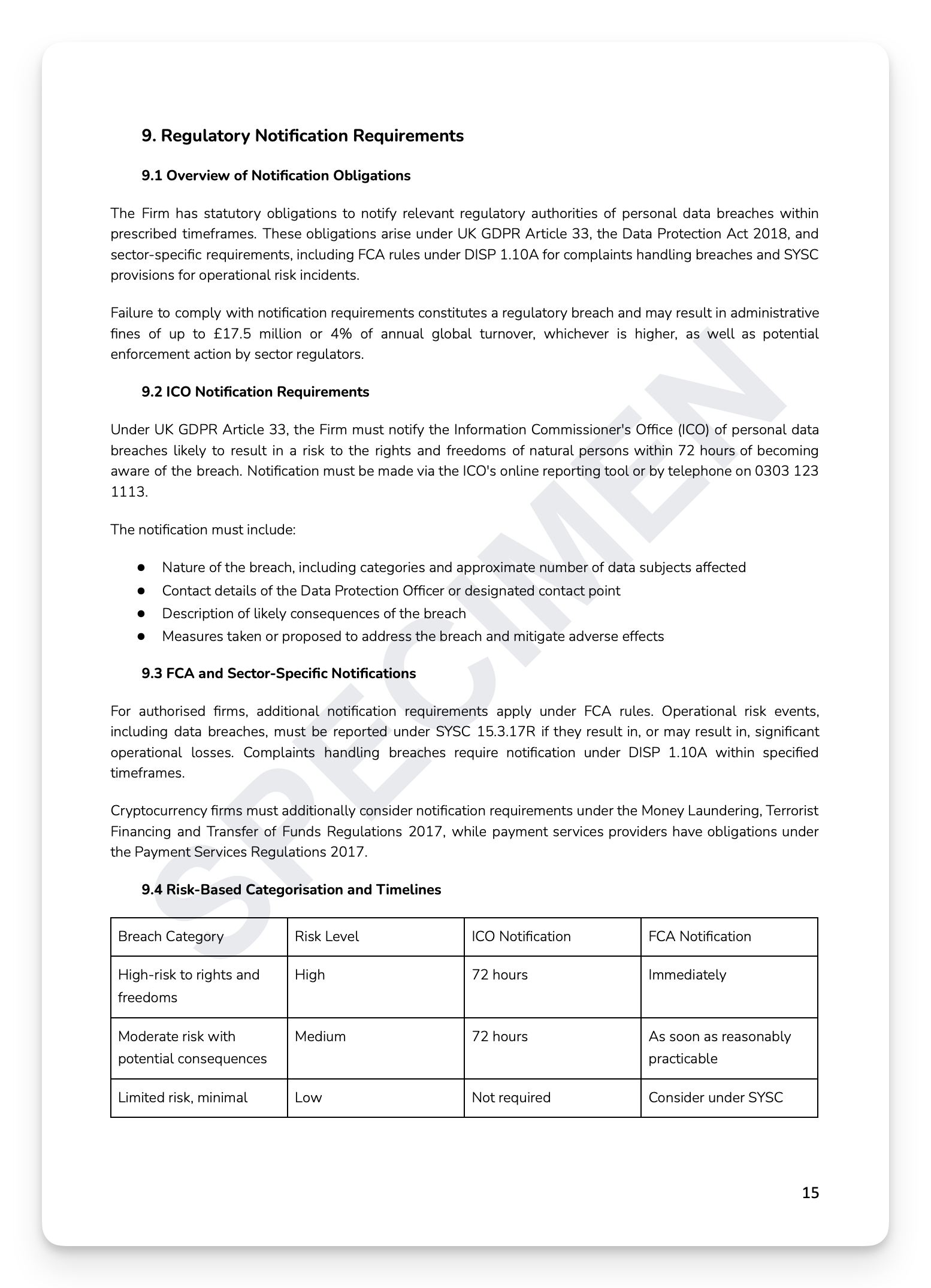 Image 6 of 7
Image 6 of 7
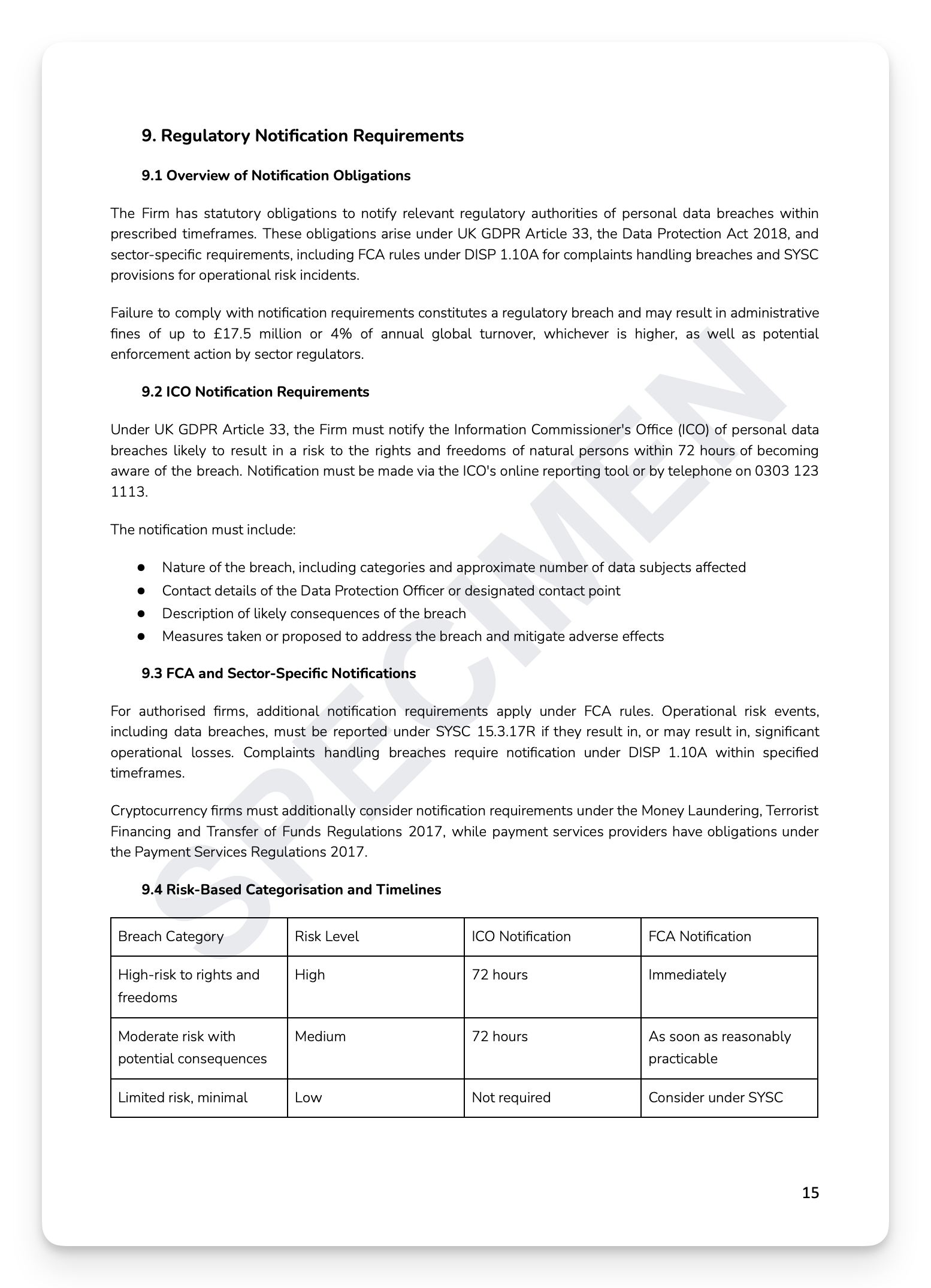
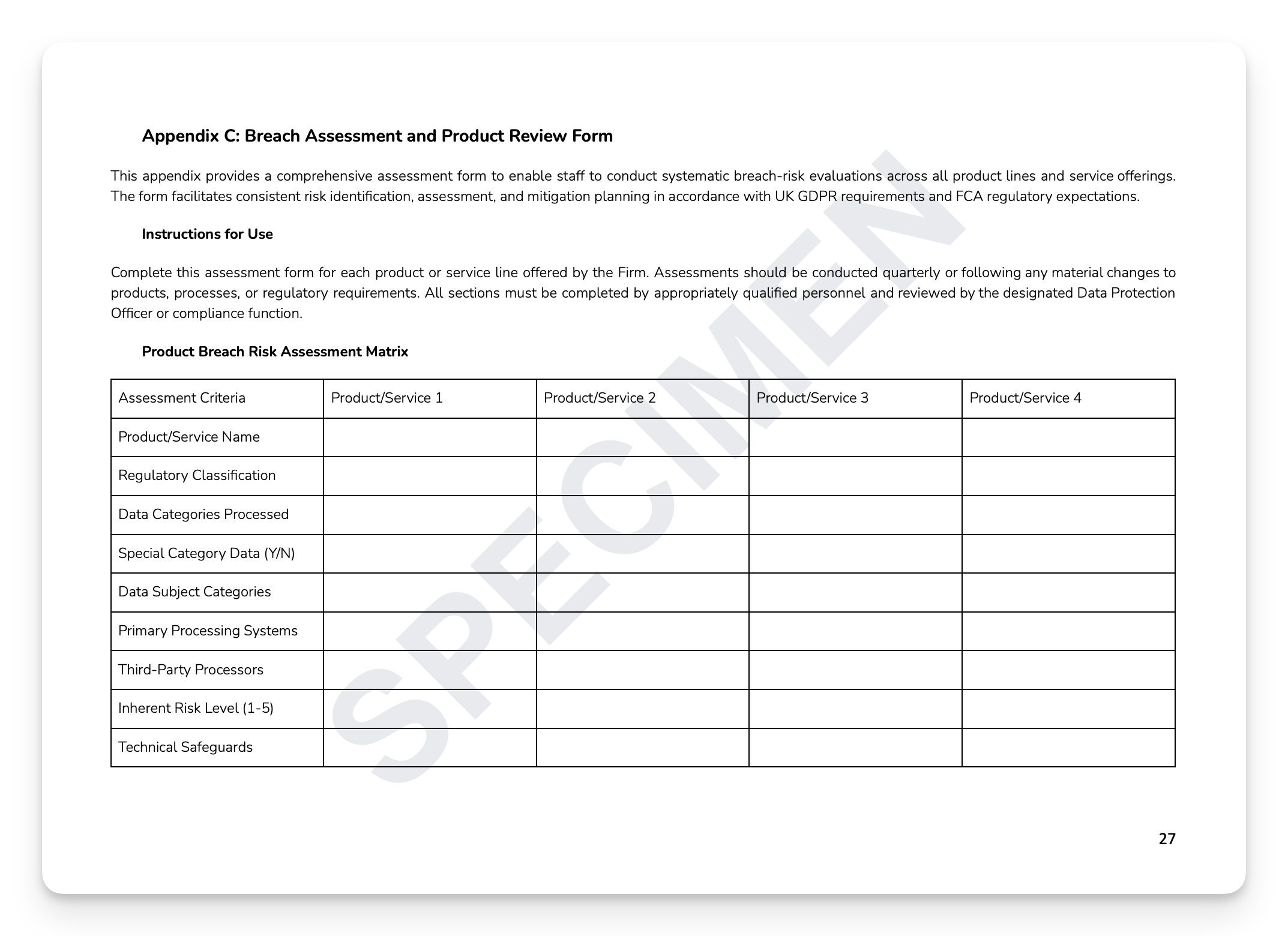 Image 7 of 7
Image 7 of 7

Data Breach Policy Template
A data breach isn't just an IT incident — it's a regulatory event with mandatory notification obligations and enforcement consequences that span both the ICO and the FCA. Under UK GDPR Article 33, firms have 72 hours to notify the ICO. The firms that navigate breaches successfully aren't the ones that avoid them — they're the ones that detect quickly, assess accurately, notify correctly, and remediate thoroughly. The FCA doesn't wait.
What's included:
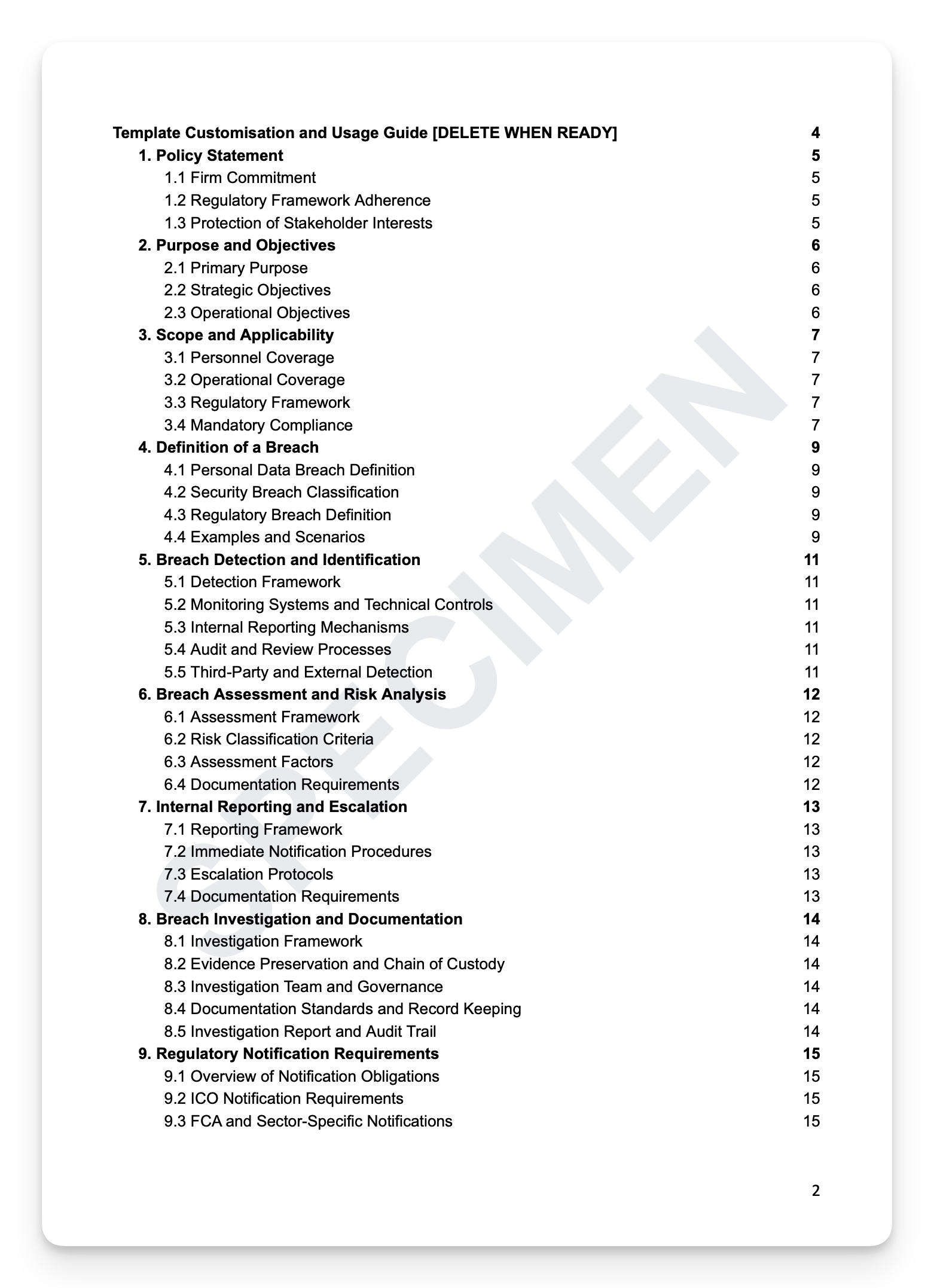
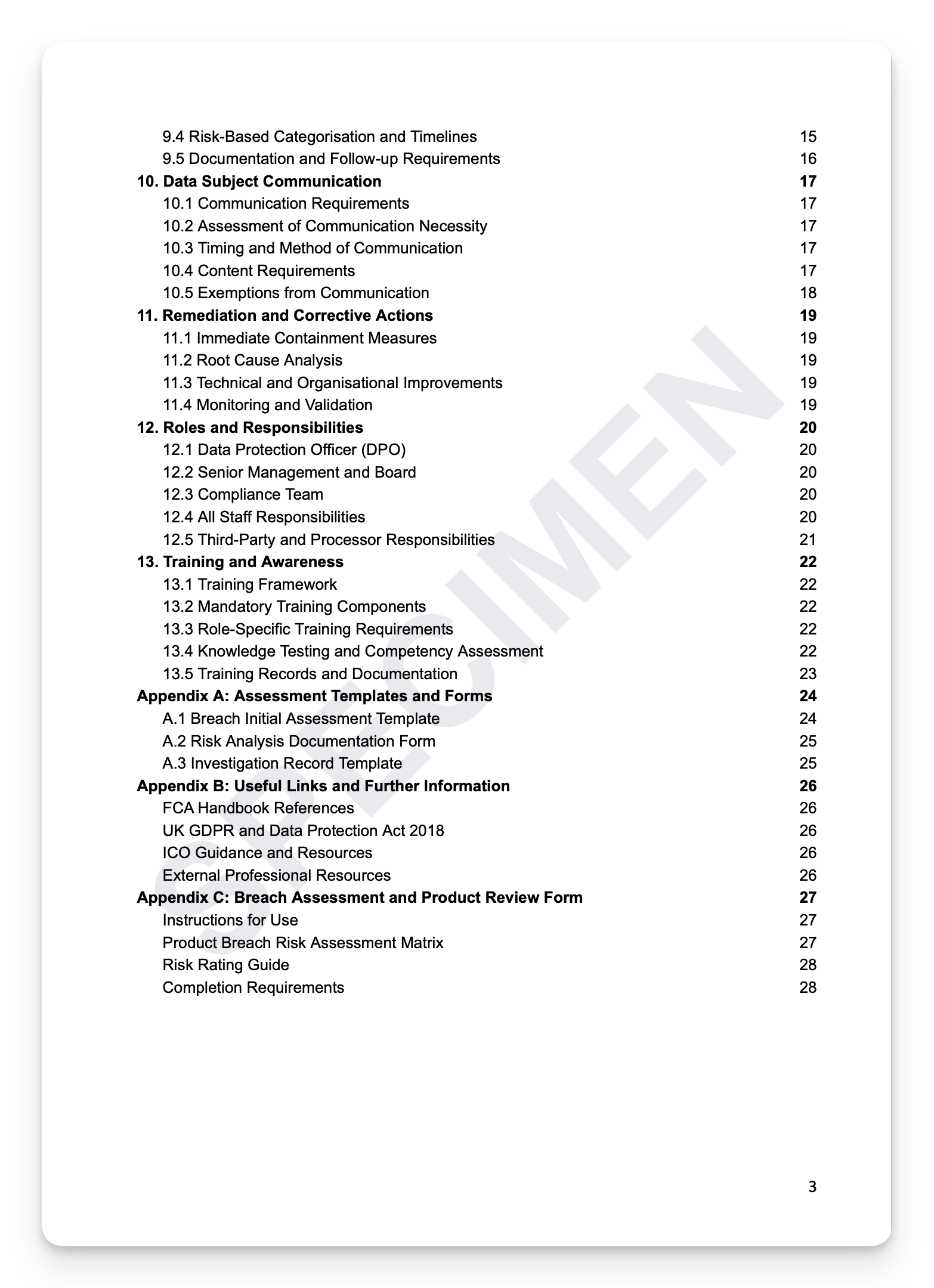
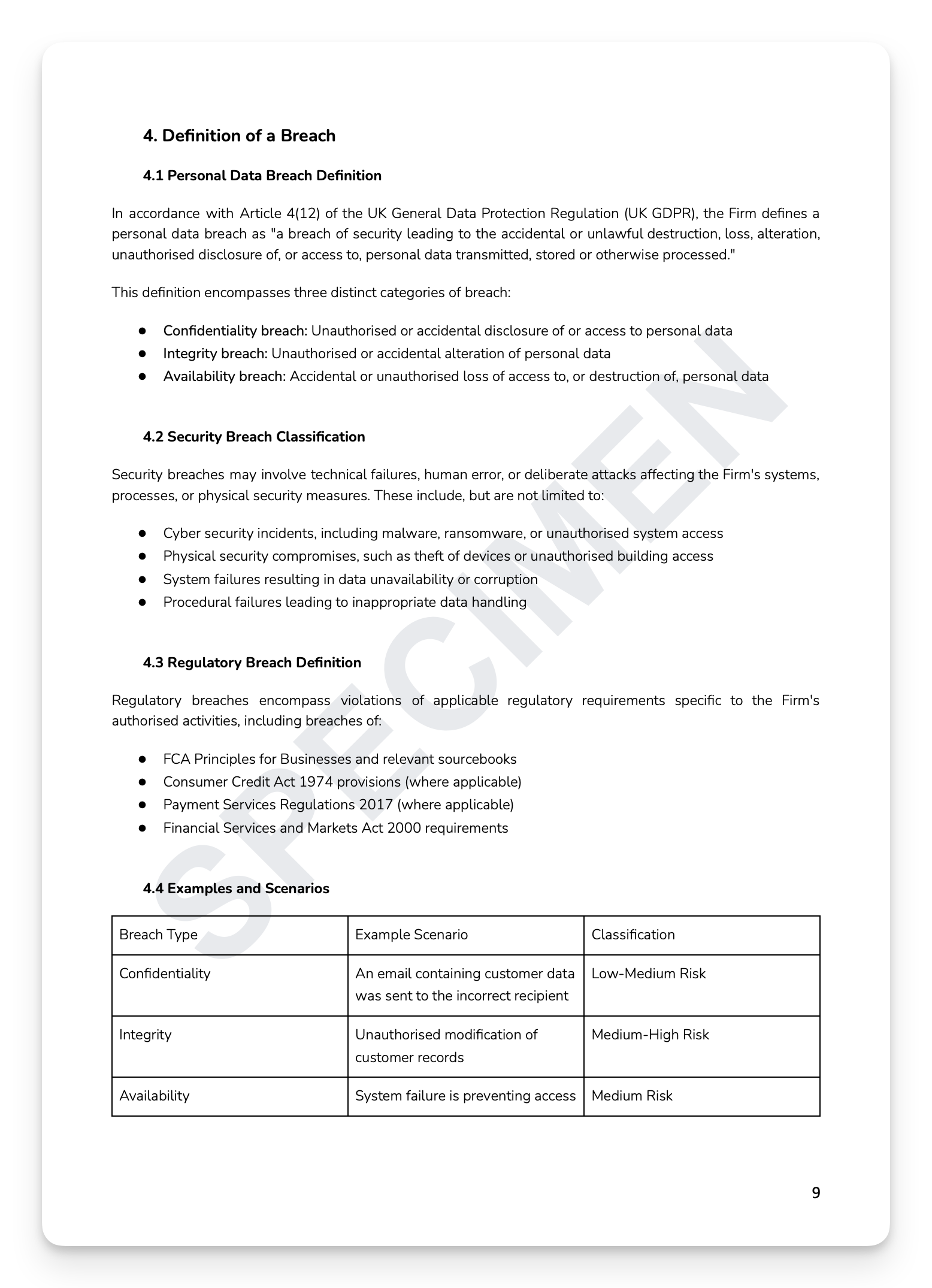
Breach definitions: personal data breach, security breach, and regulatory breach — with practical examples across all three categories
Detection and identification: monitoring systems, internal reporting mechanisms, audit processes, and third-party detection
Breach assessment and risk analysis: classification criteria, assessment factors, and documentation requirements
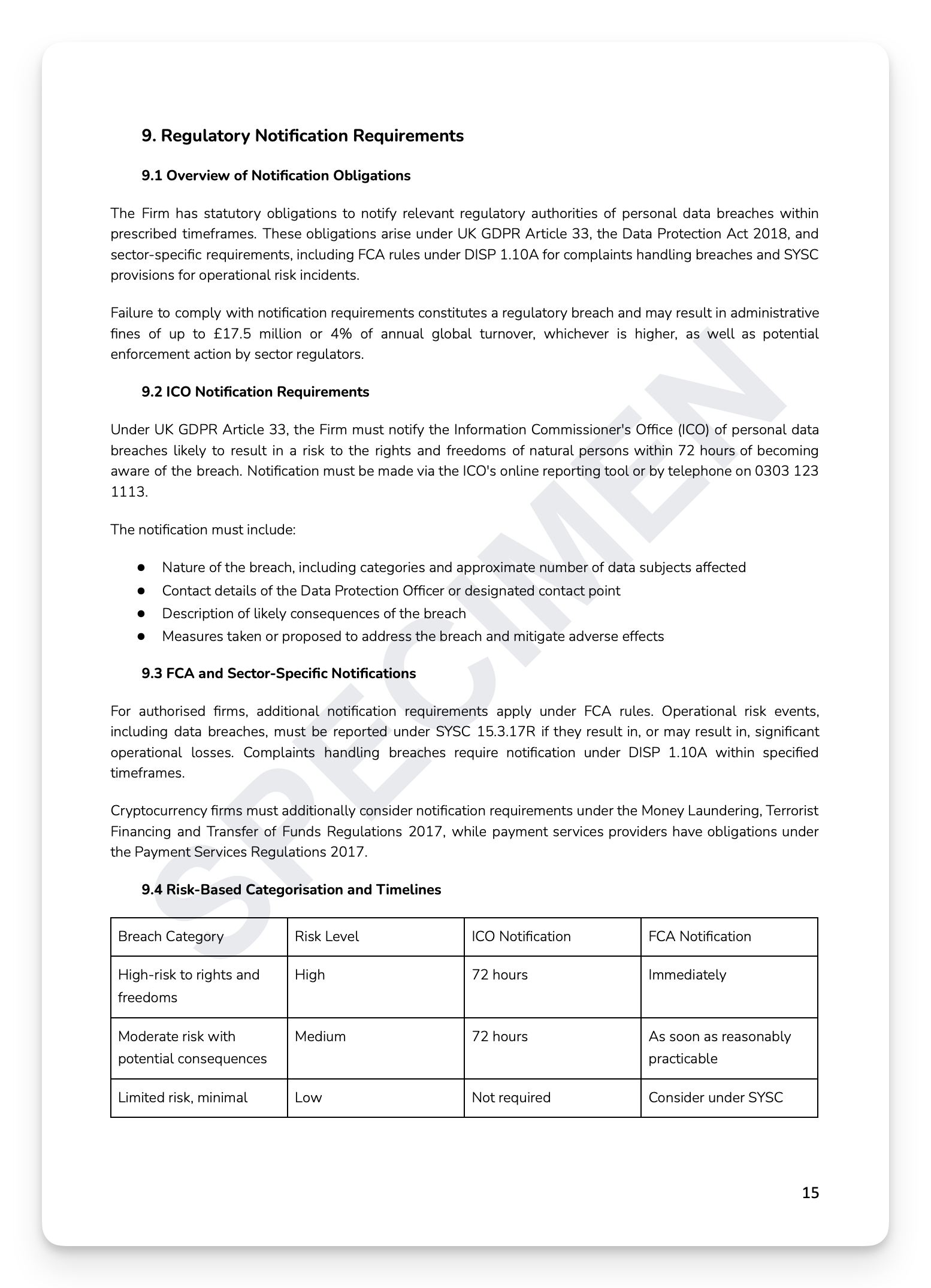
Regulatory notification: ICO 72-hour obligations, FCA sector-specific notifications, risk-based categorisation, and timelines
Data subject communication: assessment of necessity, timing and method, mandatory content, and exemptions
Remediation: immediate containment, root cause analysis, technical and organisational improvements, and monitoring
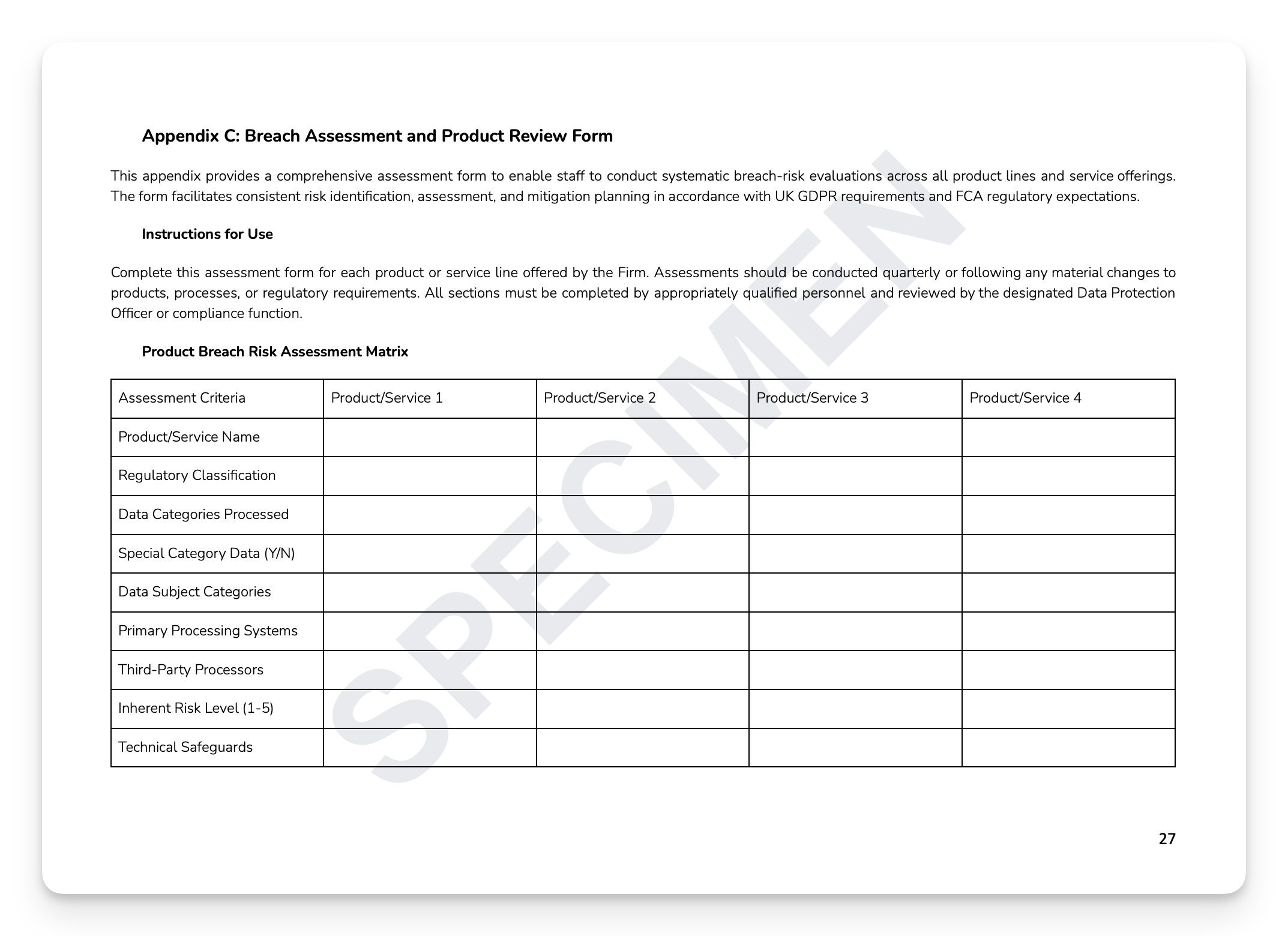
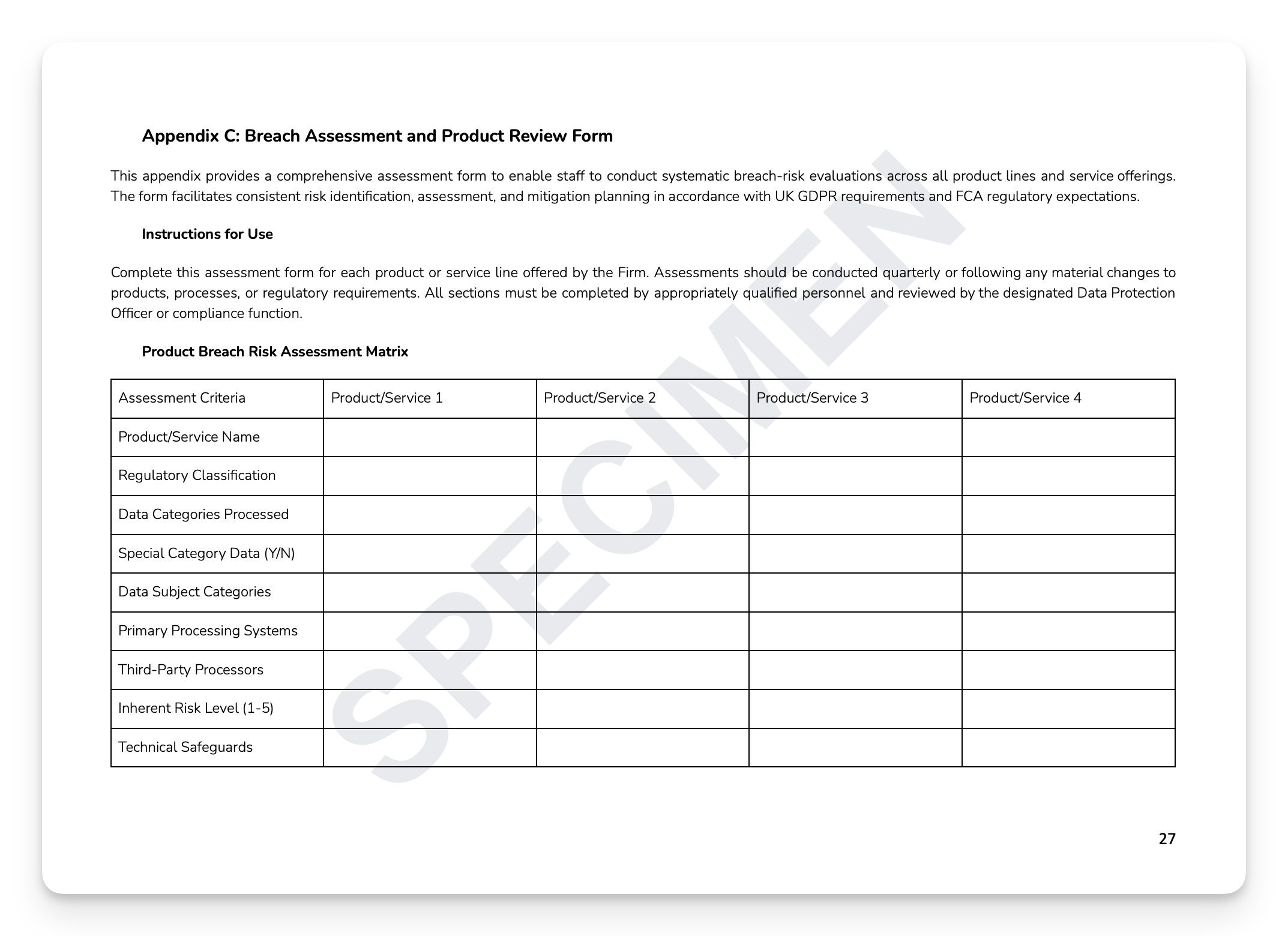
Ready-to-use appendices: Breach Initial Assessment Template, Risk Analysis Documentation Form, Investigation Record Template, and Product Breach Risk Assessment Matrix
+ much more
Who is this for?
Data Protection Officers, Compliance Officers, IT Security Managers, senior management, and Boards at FCA-regulated firms.
How it works
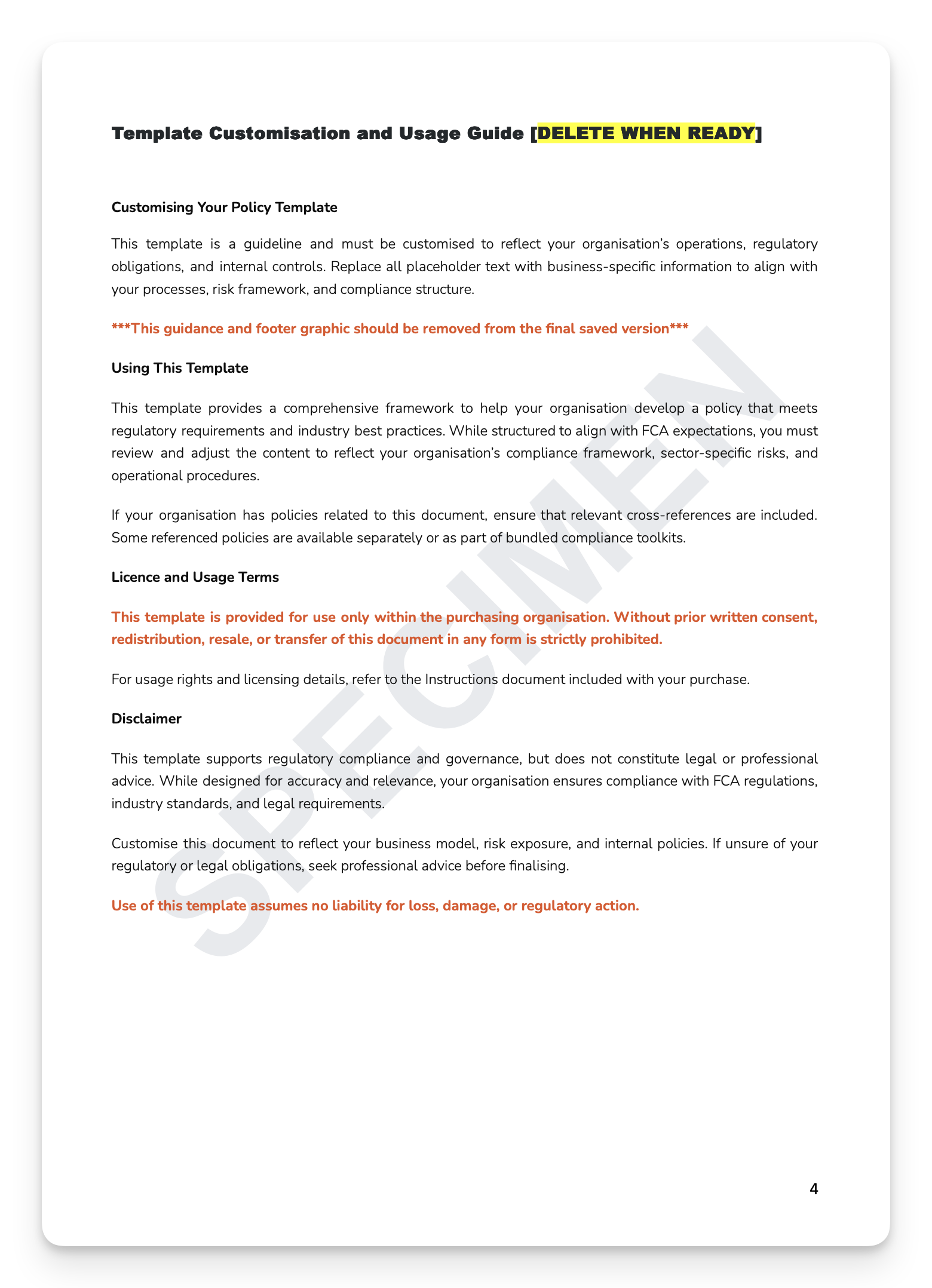
Step 1 — Read it. Every section exists for a reason, grounded in a specific regulatory obligation.
Step 2 — Understand it. Map the content against your current practices. Identify where you're strong and where gaps exist.
Step 3 — Make it yours. Tailor the language to reflect how your organisation actually operates. A policy that sounds like your firm is a policy your people will follow.
Step 4 — Take ownership. Assign clear accountability — Board approval, named SMF holder, designated policy owner. A policy without an owner is a liability, not an asset.
Step 5 — Operationalise it. Embed the policy into your governance calendar, training programme, and annual review cycle. This is where compliance becomes culture.
Or, get this free with RegTechPRO
Access this alongside the full compliance policy library — SM&CR, COBS, AML, Consumer Duty, GDPR, and more — for a fraction of the cost of consultancy.
A data breach isn't just an IT incident — it's a regulatory event with mandatory notification obligations and enforcement consequences that span both the ICO and the FCA. Under UK GDPR Article 33, firms have 72 hours to notify the ICO. The firms that navigate breaches successfully aren't the ones that avoid them — they're the ones that detect quickly, assess accurately, notify correctly, and remediate thoroughly. The FCA doesn't wait.
What's included:
Breach definitions: personal data breach, security breach, and regulatory breach — with practical examples across all three categories
Detection and identification: monitoring systems, internal reporting mechanisms, audit processes, and third-party detection
Breach assessment and risk analysis: classification criteria, assessment factors, and documentation requirements
Regulatory notification: ICO 72-hour obligations, FCA sector-specific notifications, risk-based categorisation, and timelines
Data subject communication: assessment of necessity, timing and method, mandatory content, and exemptions
Remediation: immediate containment, root cause analysis, technical and organisational improvements, and monitoring
Ready-to-use appendices: Breach Initial Assessment Template, Risk Analysis Documentation Form, Investigation Record Template, and Product Breach Risk Assessment Matrix
+ much more
Who is this for?
Data Protection Officers, Compliance Officers, IT Security Managers, senior management, and Boards at FCA-regulated firms.
How it works
Step 1 — Read it. Every section exists for a reason, grounded in a specific regulatory obligation.
Step 2 — Understand it. Map the content against your current practices. Identify where you're strong and where gaps exist.
Step 3 — Make it yours. Tailor the language to reflect how your organisation actually operates. A policy that sounds like your firm is a policy your people will follow.
Step 4 — Take ownership. Assign clear accountability — Board approval, named SMF holder, designated policy owner. A policy without an owner is a liability, not an asset.
Step 5 — Operationalise it. Embed the policy into your governance calendar, training programme, and annual review cycle. This is where compliance becomes culture.
Or, get this free with RegTechPRO
Access this alongside the full compliance policy library — SM&CR, COBS, AML, Consumer Duty, GDPR, and more — for a fraction of the cost of consultancy.